The poisonous rootkits rocking the security world
There are some seriously stealthy rootkits running on computers today. Tom Brewster investigates the extent of the problem...


Rootkits have been around for years. Born in the UNIX world over two decades ago, the term remained a part of UNIX and Linux experts' argot until the mid-2000s.
Thanks to a Sony BMG gaffe in 2005, rootkits entered the lexicon of almost everyone in the tech world. To stop people copying music excessively once installed on Windows systems, Sony ensured users didn't just download tunes when they shoved CDs into their computers, they got rootkits too.
Sony didn't appear to realise the security implications of what they were doing. By installing the Extended Copy Protection (XCP) and MediaMax CD-3 software on user systems, Sony wasn't just invading people's privacy without them knowing. It admitted the rootkit included "a feature that may make a user's computer susceptible to a virus written specifically to target the software."
Things only worsened when Sony issued its rootkit removal tool, which opened up a flaw for other malware to exploit. After all this was discovered, Sony was sued and had to recall the millions of affected CDs.
Once installed, a rootkit acts like a malware invisibility cloak.
It was one of the most significant moments in IT security history. Sony may have settled the lawsuits but the damage was done. The world now knew what rootkits were and what they were capable of. Worst of all, cyber criminals were inspired to create some seriously pernicious rootkits, some of which are leaving security companies whimpering in their labs.
The end game for cyber criminals themselves is simply to evade detection, covering up malicious software doing nasty things to infected systems.
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
"Cyber criminals are not unlike pickpockets in the real world: they try to remain as inconspicuous as possible, quietly 'working the crowds' as they target other people's property," said Kaspersky senior technology consultant David Emm. "Rootkits are a key part of the cyber criminal's armoury. Once installed, a rootkit acts like a malware invisibility cloak to hide any tell-tale signs that a malicious program is installed."
The classic kernel kits
The most concerning rootkits around today are those that target the OS kernel. "The most advanced rootkits in the wild are still kernel-based rootkits, malicious software that work from inside the operating system," said Marco Giuliani, threat research analyst at Webroot. "They are able to spread in the wild without being blocked by most security software."
The rootkit of the TDL or TDSS malware is one of the nastiest kernel-focused kits around today. Over the past three years, various versions have upped its capabilities to make it incredibly difficult to identify. It is the dark chameleon of the security world, the evil twin of Where's Wally?.
TDL-4 is the latest incarnation. It appeared in mid-2010, able to in infect both 32-bit and 64-bit operating systems, making widely-used versions of Windows vulnerable. The rootkit infects the boot sector, meaning malicious code is loaded before the operating system. To do this, TDL-4 gets into the Master Boot Record (MBR). This is what makes TDSS so stealthy.
Tom Brewster is currently an associate editor at Forbes and an award-winning journalist who covers cyber security, surveillance, and privacy. Starting his career at ITPro as a staff writer and working up to a senior staff writer role, Tom has been covering the tech industry for more than ten years and is considered one of the leading journalists in his specialism.
He is a proud alum of the University of Sheffield where he secured an undergraduate degree in English Literature before undertaking a certification from General Assembly in web development.
-
 Cleo attack victim list grows as Hertz confirms customer data stolen
Cleo attack victim list grows as Hertz confirms customer data stolenNews Hertz has confirmed it suffered a data breach as a result of the Cleo zero-day vulnerability in late 2024, with the car rental giant warning that customer data was stolen.
By Ross Kelly
-
 Lateral moves in tech: Why leaders should support employee mobility
Lateral moves in tech: Why leaders should support employee mobilityIn-depth Encouraging staff to switch roles can have long-term benefits for skills in the tech sector
By Keri Allan
-
 PowerEdge - Cyber resilient infrastructure for a Zero Trust world
PowerEdge - Cyber resilient infrastructure for a Zero Trust worldWhitepaper Combat threats with an in-depth security stance focused on data security
By ITPro
-
 Redefining modern enterprise storage for mission-critical workloads
Redefining modern enterprise storage for mission-critical workloadsWhitepaper Evolving technology to meet the mission-critical needs of the most demanding IT environments
By ITPro
-
 The business value of storage solutions from Dell Technologies
The business value of storage solutions from Dell TechnologiesWhitepaper Streamline your IT infrastructure while meeting the demands of digital transformation
By ITPro
-
 Cyber resiliency and end-user performance
Cyber resiliency and end-user performanceWhitepaper Reduce risk and deliver greater business success with cyber-resilience capabilities
By ITPro
-
 Intel Alder Lake chips safe from novel exploits following source code leak, experts say
Intel Alder Lake chips safe from novel exploits following source code leak, experts sayNews The mystery surrounding how the code was leaked is a more interesting story, experts told IT Pro, despite others branding the incident "scary"
By Rory Bathgate
-
 McAfee and Visa offer 50% off antivirus subscriptions for small businesses
McAfee and Visa offer 50% off antivirus subscriptions for small businessesNews UK Visa Classic Business card holders can access the deal starting today
By Zach Marzouk
-
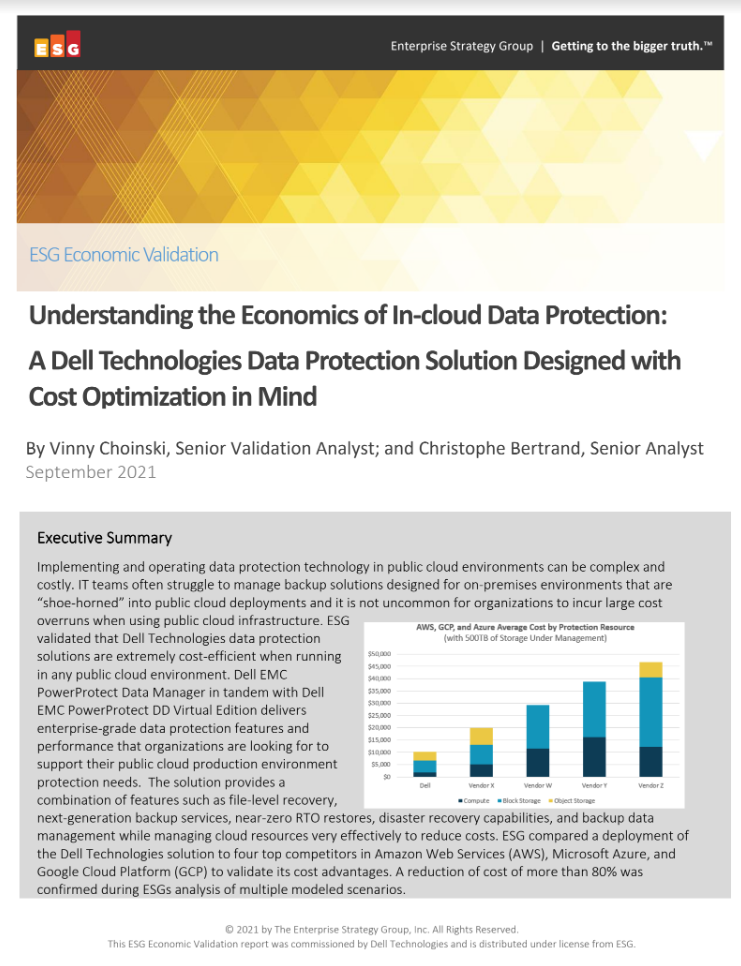 Understanding the economics of in-cloud data protection
Understanding the economics of in-cloud data protectionWhitepaper Data protection solutions designed with cost optimisation in mind
By ITPro
-
 Intel expands its bug bounty program with Project Circuit Breaker
Intel expands its bug bounty program with Project Circuit BreakerNews The initiative aims to address vulnerabilities in Intel’s firmware, GPUs, hypervisors, and chipsets
By Praharsha Anand