Symantec: Cybercriminals make £3m from ransomware
Research finds that criminal gangs are increasingly using malware to blackmail users.


Criminals are making 3 million a year from holding people's computers to ransom, according to a new study.
Research from IT security company Symantec revealed that 2.8 per cent of victims pay up to 280 to unlock computers infected with malware that locks screens and prevents them from accessing their PCs.
Cybercriminals often use social engineering tricks, such as displaying fake messages purporting to be from local police authorities, to convince victims to pay up. Such messages often include warnings such as, "you have browsed illicit materials and must pay a fine."
The research found that one gang was observed attempting to infect 495,000 computers over the course of just 18 days. The first instances of this type of cyber-attack were observed in 2009, and - until recently - it was largely limited to Russia and Eastern Europe.
"It has increasingly become a popular ploy among numerous international online criminal gangs, spreading the threat to Western Europe, the United States and Canada over the past year," said the company.
Symantec said ransomware will surpass fake anti-virus software as the leading cybercrime strategy in the coming year. It said there are other signs that ransomware is becoming increasingly professional.
Several different ransomware families, sold to what appear to be separate gangs, have all been tracked back to a single individual.
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
"That individual, who we have been unable to identify, is seemingly working full-time on programming ransomware on request" said the company.
"This dedicated development of multiple different versions of the same type of malware is reminiscent of how fake antivirus was developed."
The company also predicted that as users shift to mobile and cloud so will attackers to exploit Secure Sockets Layer (SSL) Certificates used by mobile devices and applications.
Earlier this week IT Pro reported that security researchers have identified a new malware strand that steals image files from computers and sends them to a remote server.
Rene Millman is a freelance writer and broadcaster who covers cybersecurity, AI, IoT, and the cloud. He also works as a contributing analyst at GigaOm and has previously worked as an analyst for Gartner covering the infrastructure market. He has made numerous television appearances to give his views and expertise on technology trends and companies that affect and shape our lives. You can follow Rene Millman on Twitter.
-
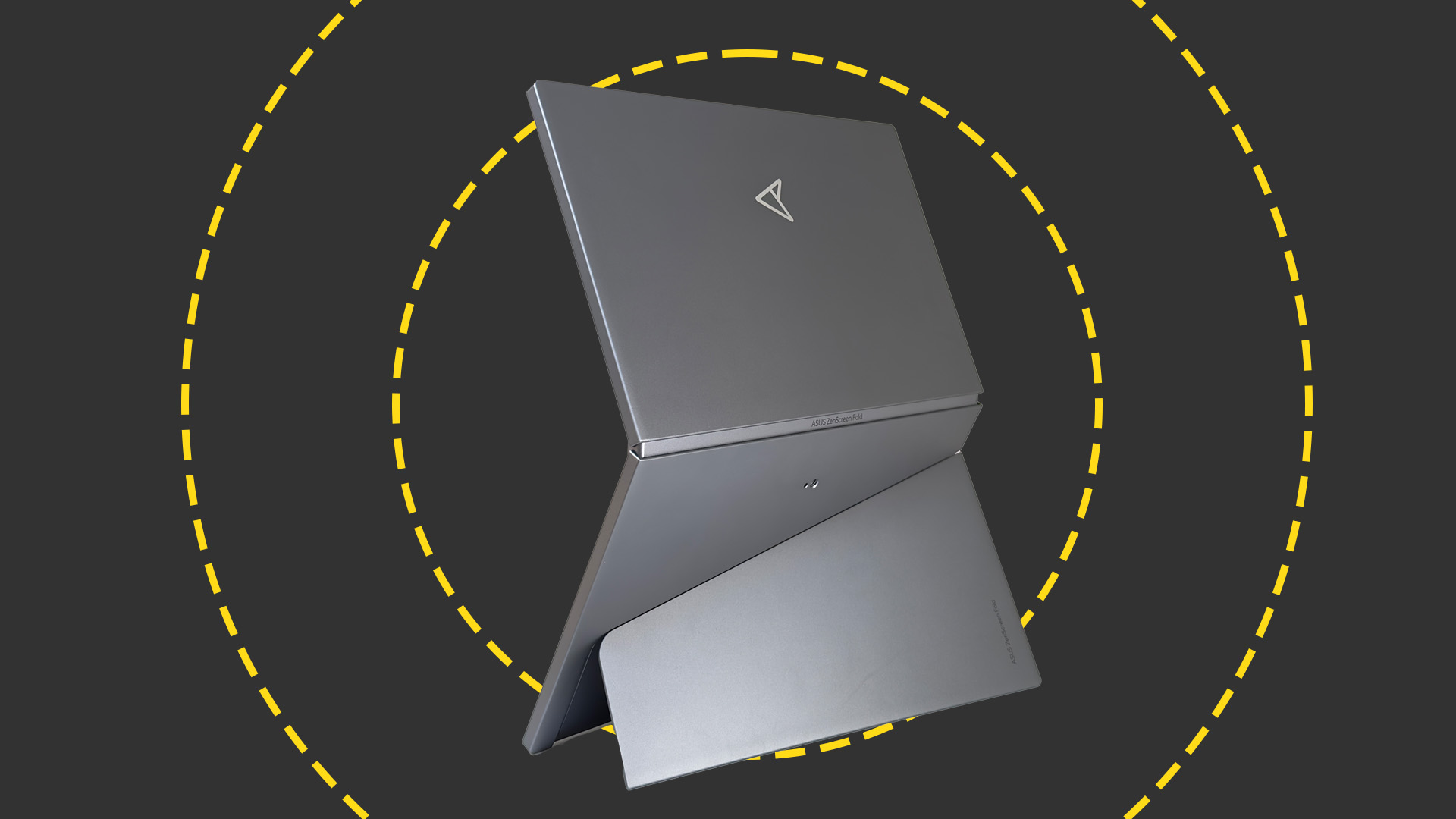 Asus ZenScreen Fold OLED MQ17QH review
Asus ZenScreen Fold OLED MQ17QH reviewReviews A stunning foldable 17.3in OLED display – but it's too expensive to be anything more than a thrilling tech demo
By Sasha Muller
-
 How the UK MoJ achieved secure networks for prisons and offices with Palo Alto Networks
How the UK MoJ achieved secure networks for prisons and offices with Palo Alto NetworksCase study Adopting zero trust is a necessity when your own users are trying to launch cyber attacks
By Rory Bathgate
-
 Cleo attack victim list grows as Hertz confirms customer data stolen – and security experts say it won't be the last
Cleo attack victim list grows as Hertz confirms customer data stolen – and security experts say it won't be the lastNews Hertz has confirmed it suffered a data breach as a result of the Cleo zero-day vulnerability in late 2024, with the car rental giant warning that customer data was stolen.
By Ross Kelly
-
 ‘Phishing kits are a force multiplier': Cheap cyber crime kits can be bought on the dark web for less than $25 – and experts warn it’s lowering the barrier of entry for amateur hackers
‘Phishing kits are a force multiplier': Cheap cyber crime kits can be bought on the dark web for less than $25 – and experts warn it’s lowering the barrier of entry for amateur hackersNews Research from NordVPN shows phishing kits are now widely available on the dark web and via messaging apps like Telegram, and are often selling for less than $25.
By Emma Woollacott
-
 Healthcare systems are rife with exploits — and ransomware gangs have noticed
Healthcare systems are rife with exploits — and ransomware gangs have noticedNews Nearly nine-in-ten healthcare organizations have medical devices that are vulnerable to exploits, and ransomware groups are taking notice.
By Nicole Kobie
-
 Alleged LockBit developer extradited to the US
Alleged LockBit developer extradited to the USNews A Russian-Israeli man has been extradited to the US amid accusations of being a key LockBit ransomware developer.
By Emma Woollacott
-
 February was the worst month on record for ransomware attacks – and one threat group had a field day
February was the worst month on record for ransomware attacks – and one threat group had a field dayNews February 2025 was the worst month on record for the number of ransomware attacks, according to new research from Bitdefender.
By Emma Woollacott
-
 CISA issues warning over Medusa ransomware after 300 victims from critical sectors impacted
CISA issues warning over Medusa ransomware after 300 victims from critical sectors impactedNews The Medusa ransomware as a Service operation compromised twice as many organizations at the start of 2025 compared to 2024
By Solomon Klappholz
-
 Warning issued over prolific 'Ghost' ransomware group
Warning issued over prolific 'Ghost' ransomware groupNews The Ghost ransomware group is known to act fast and exploit vulnerabilities in public-facing appliances
By Solomon Klappholz
-
 The Zservers takedown is another big win for law enforcement
The Zservers takedown is another big win for law enforcementNews LockBit has been dealt another blow by law enforcement after Dutch police took 127 of its servers offline
By Solomon Klappholz