Mirai 'botmasters' now exploiting Hadoop flaw to target Linux servers
Malware used to take half the internet offline is being used to build powerful botnets with just a handful of compromised servers

Cyber criminals who used a botnet malware that took large parts of the internet offline in 2016 are now abusing Linux servers at scale.
Mirai, an open source malware, was conventionally used to target Internet of Things (IoT) devices like wireless cameras and routers. Malicious actors infamously used Mirai to construct a botnet that led to a devastating distributed denial of service (DDoS) attack against major online platforms.
But researchers have found evidence that certain strains are now targeting Linux servers, with a handful of attackers using custom tools to exploit a Hadoop YARN vulnerability and deliver malware instead of relying on bots to spread.
This is the first time security researchers have spotted non-IoT Mirai "in the wild", according to Network performance management firm Netscout.
"Mirai is no longer solely targeting IoT devices. While the techniques used to deliver Mirai to both IoT and Linux servers may be similar, it's much easier for attackers to attack the x86 monoculture of Linux servers than the wide array of CPUs used in IoT devices," said Netscout researcher Matthew Bing.
"The limited number of sources we've seen continually scanning for the Hadoop YARN vulnerability may indicate this activity is the work of a small group of attackers. Their goal is clear - to install the malware on as many devices as possible."
YARN (Yet Another Resource Negotiator) is a technology deployed as a resource management and job scheduling system for Apache Hadoop. It's responsible for allocating system resources to various applications running a Hadoop cluster, as well as scheduling tasks to execute on different nodes.
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
The vulnerability manifests as a command injection flaw that allows an attacker to execute arbitrary shell commands and resembles many flaws seen in IoT devices. It's for this reason Mirai attackers see Linux servers as a viable target.
His team's global network of 'honeypot' servers of recorded tens of thousands of attempts to exploit the vulnerability per day, indicating the flaw is being abused "at scale", with attackers sending exploits to as many vulnerable servers as they possibly can.
"Once gaining a foothold, Mirai on a Linux server behaves much like an IoT bot and begins brute-forcing telnet usernames and passwords," Bing continued.
"What's different now is that among the small, diminutive devices in the botnet lurk fully powered Linux servers."
Data centre-based Linux servers present a greater opportunity to launch DDoS attacks as they have more bandwidth than IoT devices, he explained, with attackers able to build a powerful botnet from just a handful of servers.
Mirai was behind one of the most disruptive DDoS attacks the world has sustained, with cyber criminals sending tens of millions of access requests to domain name system (DNS) provider Dyn from compromised IoT devices.
Dyn is used by a host of industry giants like Twitter, Spotify and Github to name a few, meaning all these services were taken offline when the DNS provider was targeted.

Keumars Afifi-Sabet is a writer and editor that specialises in public sector, cyber security, and cloud computing. He first joined ITPro as a staff writer in April 2018 and eventually became its Features Editor. Although a regular contributor to other tech sites in the past, these days you will find Keumars on LiveScience, where he runs its Technology section.
-
 Bigger salaries, more burnout: Is the CISO role in crisis?
Bigger salaries, more burnout: Is the CISO role in crisis?In-depth CISOs are more stressed than ever before – but why is this and what can be done?
By Kate O'Flaherty Published
-
 Cheap cyber crime kits can be bought on the dark web for less than $25
Cheap cyber crime kits can be bought on the dark web for less than $25News Research from NordVPN shows phishing kits are now widely available on the dark web and via messaging apps like Telegram, and are often selling for less than $25.
By Emma Woollacott Published
-
 Seized database helps Europol snare botnet customers in ‘Operation Endgame’ follow-up sting
Seized database helps Europol snare botnet customers in ‘Operation Endgame’ follow-up stingNews Europol has detained several people believed to be involved in a botnet operation as part of a follow-up to a major takedown last year.
By Emma Woollacott Published
-
 Busting nine myths about file-based threats
Busting nine myths about file-based threatsWhitepaper Distinguish the difference between fact and fiction when it comes to preventing file-based threats
By ITPro Published
-
 The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standard
The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standardWhitepaper Cost savings and business benefits enabled by the Intel vPro® Platform as an endpotnt standard
By ITPro Published
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Cost savings and business benefits enabled by MaaS360
By ITPro Published
-
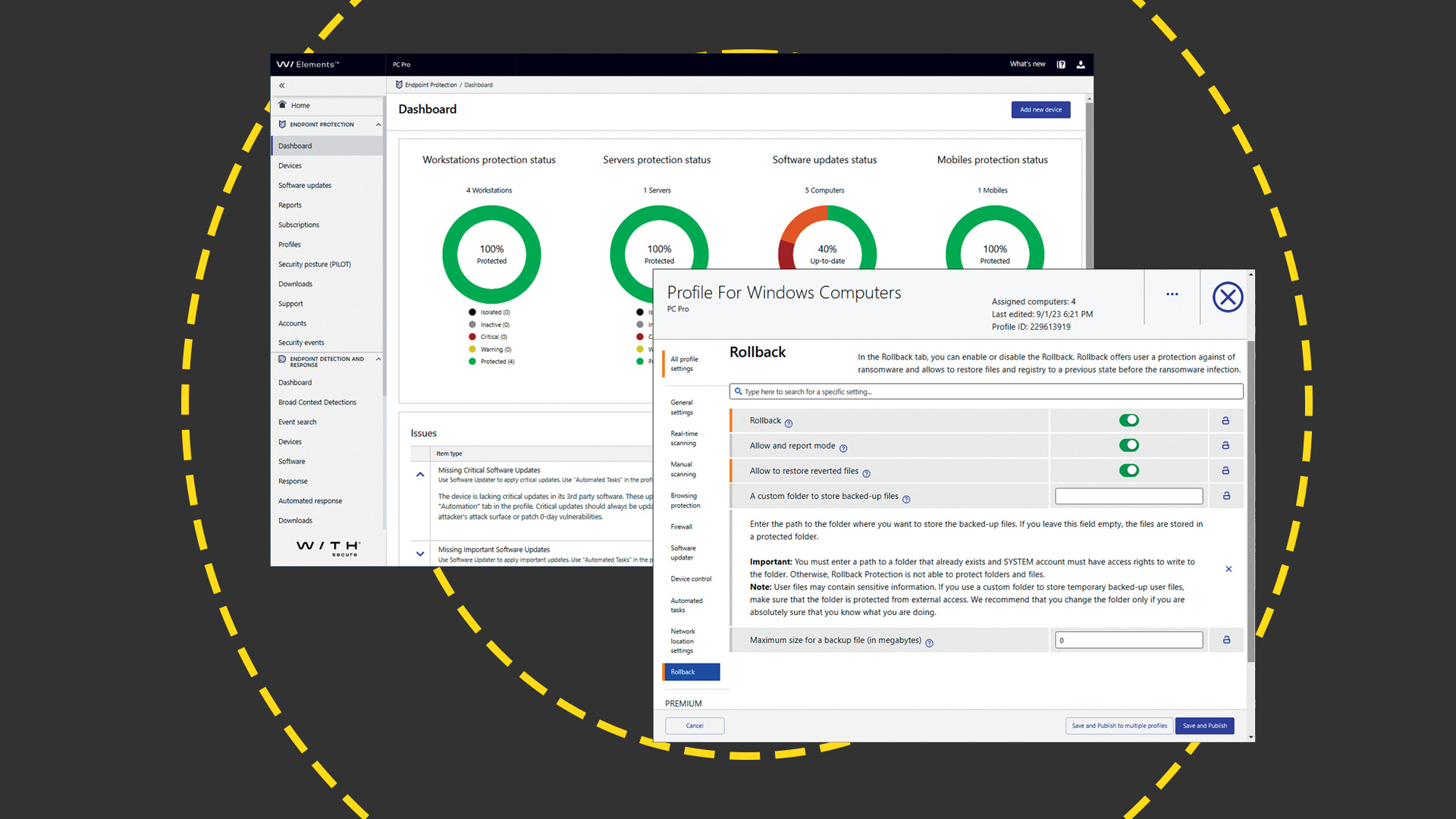 WithSecure Elements EPP and EDR review: Endpoint protection on a plate
WithSecure Elements EPP and EDR review: Endpoint protection on a plateReviews An affordable cloud-managed solution with smart automated remediation services
By Dave Mitchell Published
-
 KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023
KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023Whitepaper Get an updated overview of vendors and their product offerings in the UEM market.
By ITPro Published
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Get a framework to evaluate the potential financial impact of the MaaS360 on your organization
By ITPro Published
-
 Unified endpoint management software vendor assessment
Unified endpoint management software vendor assessmentWhitepaper Make positive steps on your intelligent automation journey
By ITPro Published