Google Cloud's Security Command Centre enters beta phase
The new dashboard aims to streamline the detection and remedying of security threats across its cloud product range


Google Cloud has announced its Cloud Security Command Centre (SCC), previously revealed back in March, is now available in beta to Google Cloud Platform (GCP) customers.
The Cloud SCC, according to Google Cloud, is the first of its kind to be offered by a major cloud provider which offers organization-level visibility into assets, vulnerabilities, and threats. Essentially, the new service provides a user-friendly hub for all levels of a business to access and assess data security events from across its network.
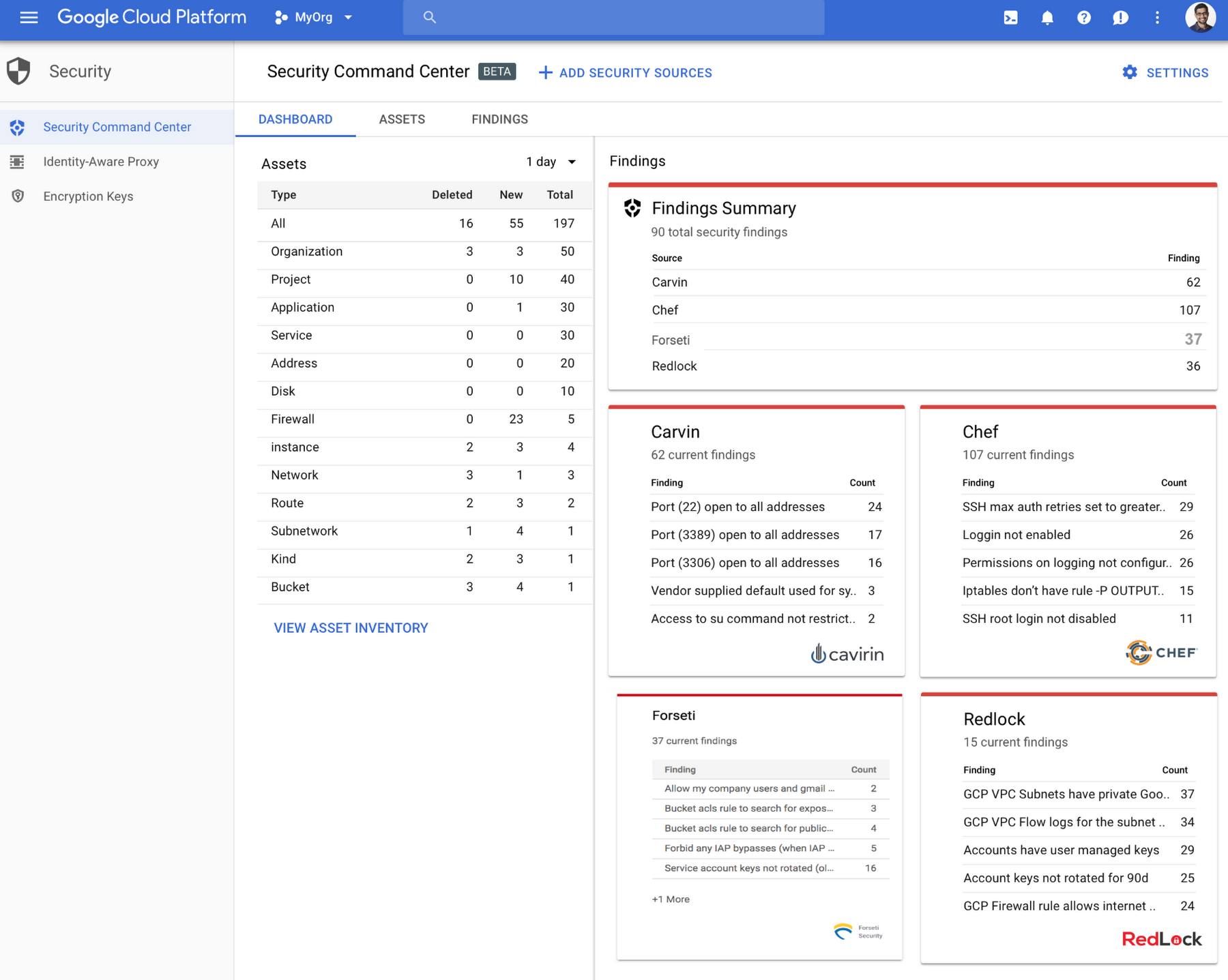
Data can be accessed through a simple dashboard which allows for fast detection of security risks and possible vulnerabilities. This can include overly permissive firewalls and alerts relating to possible compromise leading to coin mining.
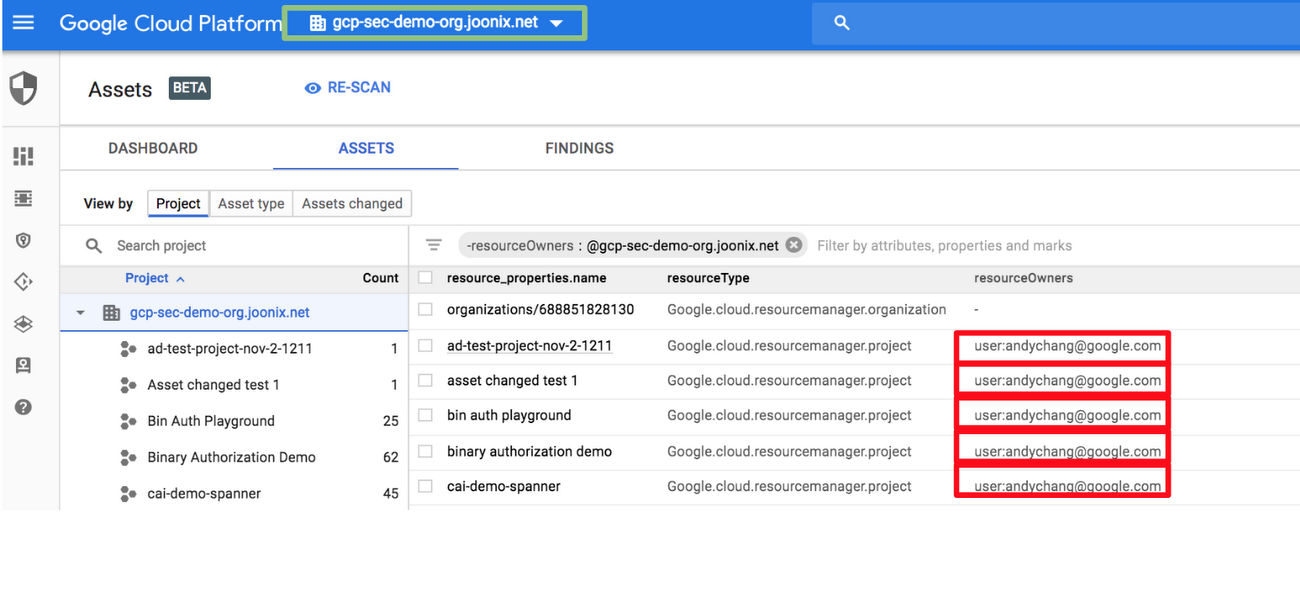
The Cloud SCC gives users a comprehensive overview of all cloud assets across GCP services, allowing the viewing of resources across the whole GCP organisation or for just specific projects. It also allows users to make changes such as setting up automatic notifications after a policy change is made to a network firewall, which then needs to be reverted at a late date.
Another interesting feature about the Cloud SCC is that it provides an overview of not just Google Cloud security services such as Foresti and Cloud Security Scanner, but for third-party services too if the business has those implemented alongside Google Cloud services.
The features also work to streamline the experience of detecting security risks in the business by having all assets feed information into one dashboard, without having to visit separate consoles or cloud environments. Third-party tools can also be directly accessed through Cloud SCC to help speed remediation efforts.
The SCC will also provide coverage across Cloud Datastore, Cloud DNS, Cloud Load Balancing, Cloud Spanner, Container Registry, Kubernetes Engine, and Virtual Private Cloud, the company confirmed.
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
The tool is similar in function to the Shield platform currently being developed by Box, announced in August. Box is betting on machine learning-based security as a major selling point of the platform, which will also give admins a detailed overview of a company's security portfolio.
Set to be released in 2019, Box Shield will allow security analysts to check to see what content is being accessed, who is accessing it, and whether sensitive data is being downloaded.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Bigger salaries, more burnout: Is the CISO role in crisis?
Bigger salaries, more burnout: Is the CISO role in crisis?In-depth CISOs are more stressed than ever before – but why is this and what can be done?
By Kate O'Flaherty Published
-
 Cheap cyber crime kits can be bought on the dark web for less than $25
Cheap cyber crime kits can be bought on the dark web for less than $25News Research from NordVPN shows phishing kits are now widely available on the dark web and via messaging apps like Telegram, and are often selling for less than $25.
By Emma Woollacott Published
-
 Maximizing Microsoft 365 Security: How Cloudflare enhances protection and adds value
Maximizing Microsoft 365 Security: How Cloudflare enhances protection and adds valueWebinar Strengthen your defenses, proactively block attacks, and reduce risks
By ITPro Published
-
 VPN replacement phases: Learn others’ real-world approaches
VPN replacement phases: Learn others’ real-world approachesWebinar Accelerate Zero Trust adoption
By ITPro Published
-
 Understanding NIS2 directives: The role of SASE and Zero Trust
Understanding NIS2 directives: The role of SASE and Zero TrustWebinar Enhance cybersecurity measures to comply with new regulations
By ITPro Published
-
 From legacy to leading edge: Transforming app delivery for better user experiences
From legacy to leading edge: Transforming app delivery for better user experiencesWebinar Meet end-user demands for high-performing applications
By ITPro Published
-
 Navigating evolving regional data compliance and localization regulations with Porsche Informatik
Navigating evolving regional data compliance and localization regulations with Porsche InformatikWebinar A data localization guide for enterprises
By ITPro Published
-
 Strategies for improving security team efficiency
Strategies for improving security team efficiencyWebinar Get more value from your digital investments
By ITPro Last updated
-
 Understanding NIS2 directives: The role of SASE and Zero Trust
Understanding NIS2 directives: The role of SASE and Zero TrustWebinar Enhance cybersecurity measures to comply with new regulations
By ITPro Published
-
 Navigating evolving regional data compliance and localization regulations with Porsche Informatik
Navigating evolving regional data compliance and localization regulations with Porsche InformatikWebinar A data localization guide for enterprises
By ITPro Published