FBI investigating Juniper's security breach
The investigatory department is worried foreign governments could use the flaw to hack into its systems
The FBI is investigating Juniper Networks' software breach after it came to light criminals were infiltrating VPN networks, allowing them to eavesdrop on VPN connections.
The US government is concerned the hole could be used by hackers working for foreign governments to hack into its systems and those of private businesses using a back door flaw. In fact, some officials think a foreign government (either Russia or China) set it up because it is such a sophisticated way of breaking into a network.
One FBI official said the hole was the same as "stealing a master key to get into any government building," when referring to its severity, CNN reports.
A senior administration official told the news outlet, "We are aware of the vulnerabilities recently announced by Juniper. The Department of Homeland Security has been and remains in close touch with the company. The administration remains committed to enhancing our national cybersecurity by raising our cyber defenses, disrupting adversary activity, and effectively responding to incidents when they occur."
Juniper Networks firm said it discovered the problem during a "recent code review", although it did not say how the backdoor occurred or how long it had been present.
"A skilled attacker would likely remove these entries from the local log file, thus effectively eliminating any reliable signature that the device had been compromised," Juniper said in the software update.
Juniper has since issued a software update that it says closed the hole, so hackers were no longer able to break into the systems.
According to a blog posting, Bob Worrall, senior vice president and chief information officer said that the company found "unauthorized code in ScreenOS that could allow a knowledgeable attacker to gain administrative access to NetScreen devices and to decrypt VPN connections".
"Once we identified these vulnerabilities, we launched an investigation into the matter, and worked to develop and issue patched releases for the latest versions of ScreenOS," he said.
He added that the firm had not received any reports of these vulnerabilities being exploited. "However, we strongly recommend that customers update their systems and apply the patched releases with the highest priority."
Worrall said further information about the update can be found the company's Security Incident Response website.
The security advisory described how a hacker could gain unauthorised remote administrative access to the device over SSH or telnet. "Exploitation of this vulnerability can lead to complete compromise of the affected system," the advisory stated.
"Upon exploitation of this vulnerability, the log file would contain an entry that system' had logged on followed by password authentication for a username."
The advisory noted that a skilled attacker would likely remove these entries from the log file, thus effectively eliminating any reliable signature that the device had been compromised.
A second issue may allow a knowledgeable attacker who can monitor VPN traffic to decrypt that traffic. It is independent of the first issue.
"There is no way to detect that this vulnerability was exploited," it said.
This article was originally published on 18/12/15 and has been updated (most recently on 22/12/15) to reflect new information.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Rene Millman is a freelance writer and broadcaster who covers cybersecurity, AI, IoT, and the cloud. He also works as a contributing analyst at GigaOm and has previously worked as an analyst for Gartner covering the infrastructure market. He has made numerous television appearances to give his views and expertise on technology trends and companies that affect and shape our lives. You can follow Rene Millman on Twitter.
-
 TPUs: Google's home advantage
TPUs: Google's home advantageITPro Podcast How does TPU v7 stack up against Nvidia's latest chips – and can Google scale AI using only its own supply?
-
 Microsoft Excel is still alive and kicking at 40
Microsoft Excel is still alive and kicking at 40News A recent survey found Gen Z and Millennial finance professionals have a strong “emotional attachment” to Microsoft Excel
-
 Microsoft is ending support for the Remote Desktop app – here are three alternatives you can try instead
Microsoft is ending support for the Remote Desktop app – here are three alternatives you can try insteadNews Microsoft has announced plans to end support for its Remote Desktop application in just over two months.
-
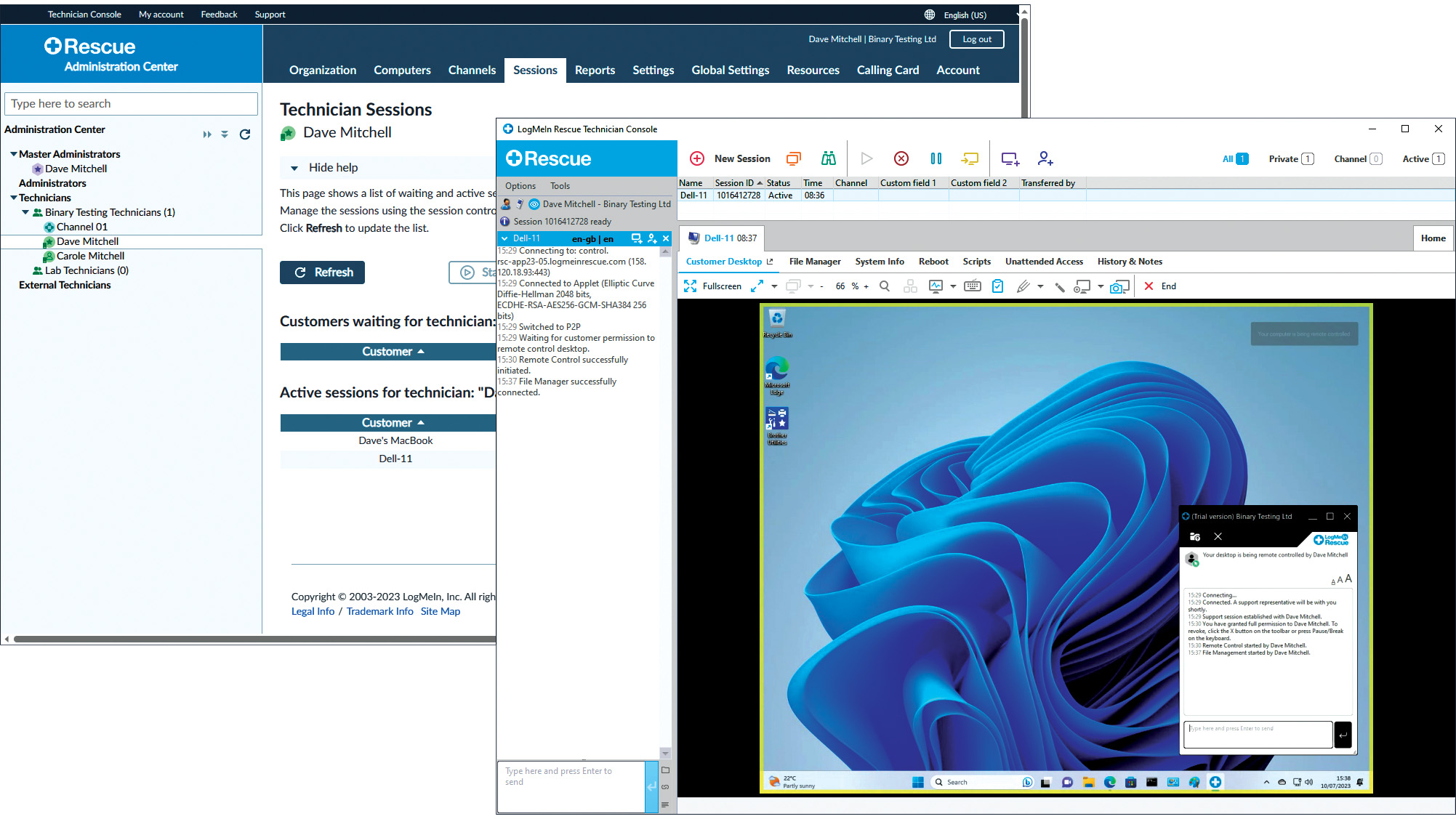 LogMeIn Rescue review: For those who want the strictest access security for their remote support services
LogMeIn Rescue review: For those who want the strictest access security for their remote support servicesReviews LogMeIn Rescue delivers an easily deployed cloud-hosted support solution with top-notch access security
-
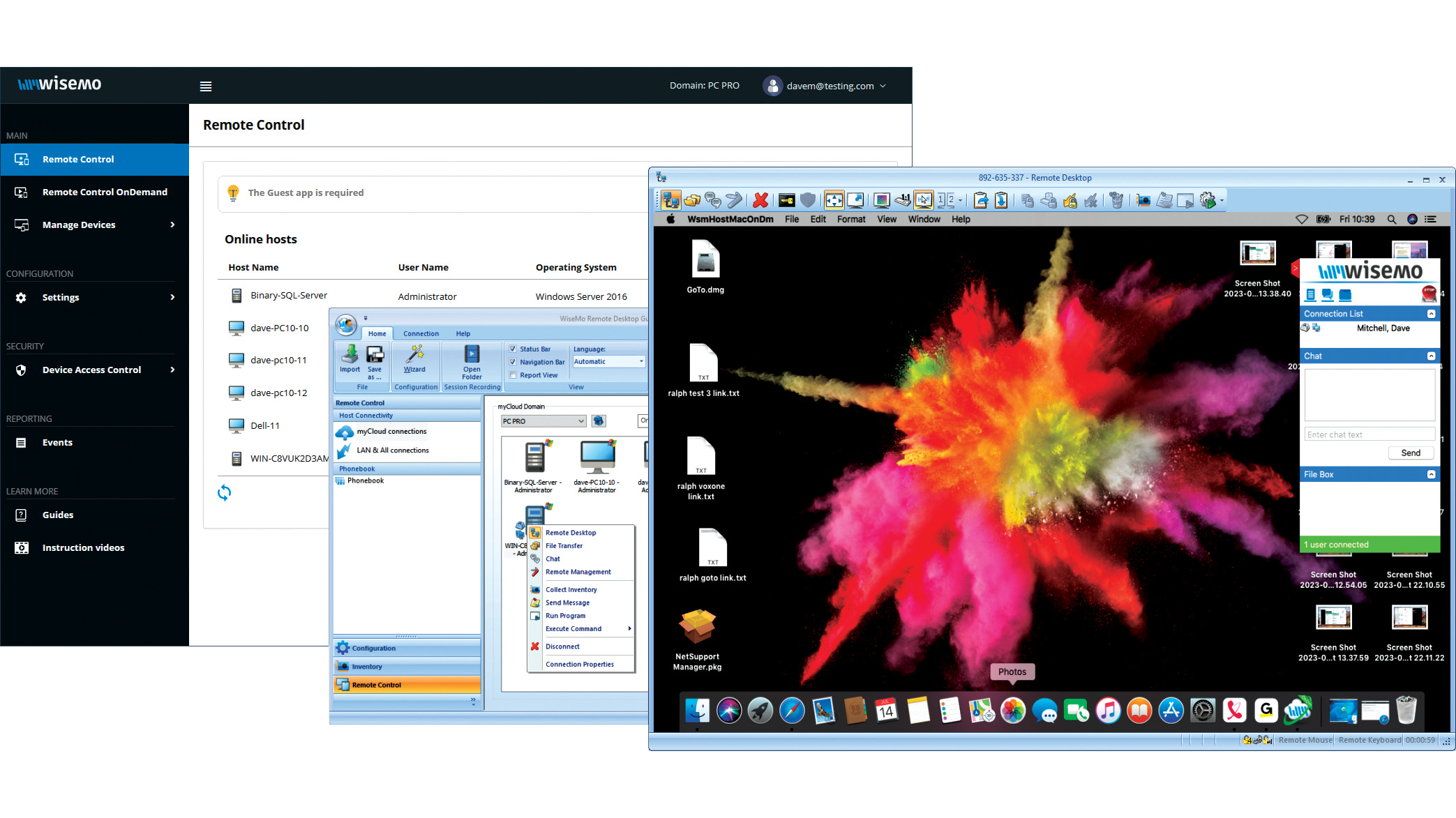 Wisemo Remote Control review: Ideal for businesses that want versatile connection options
Wisemo Remote Control review: Ideal for businesses that want versatile connection optionsReviews A smart hybrid support solution with great access security and a connection for every occasion
-
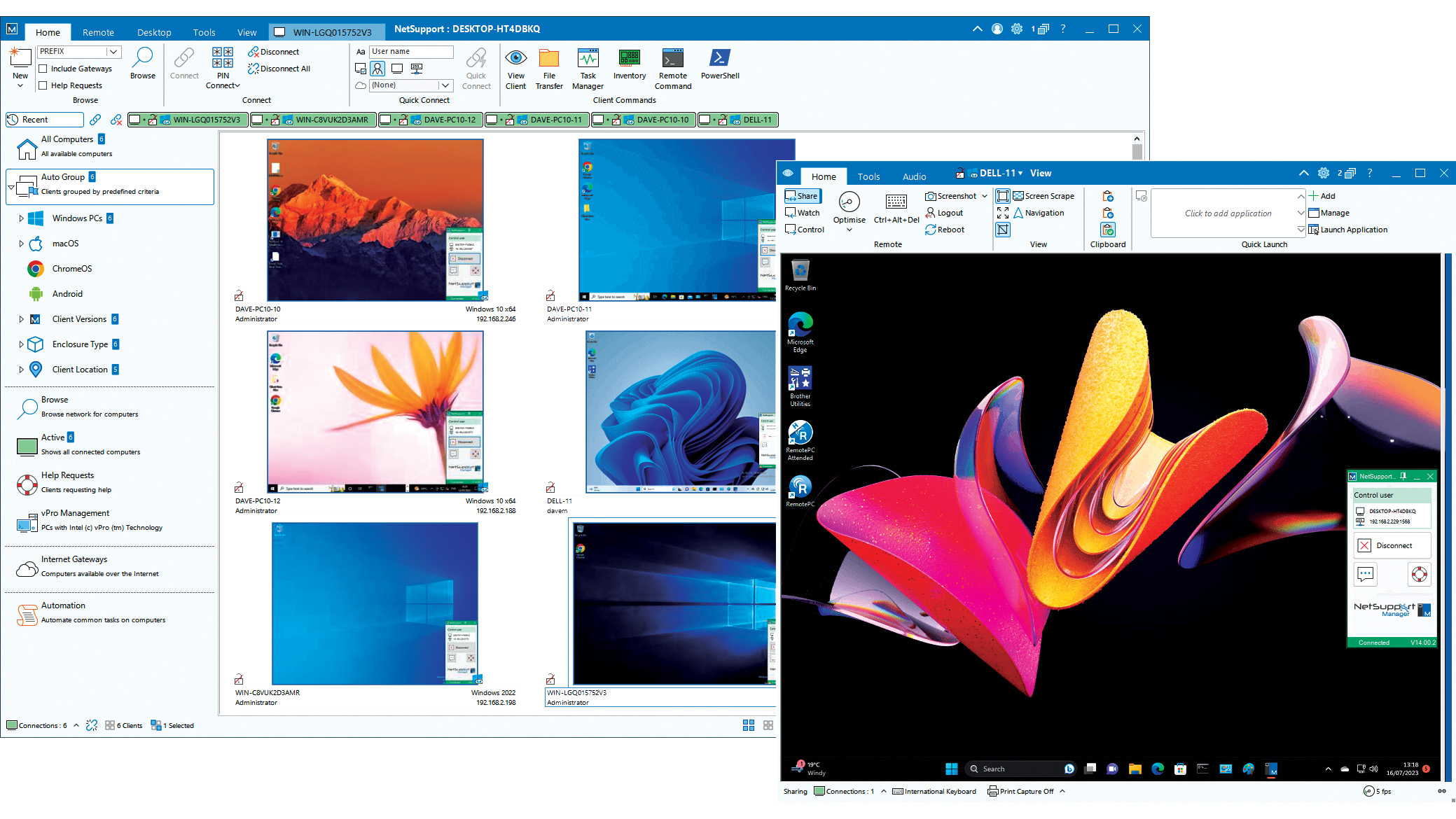 NetSupport Manager 14 review: Delivers a wealth of support tools
NetSupport Manager 14 review: Delivers a wealth of support toolsReviews The perfect on-premises support solution with a wealth of valuable features and simple licensing
-
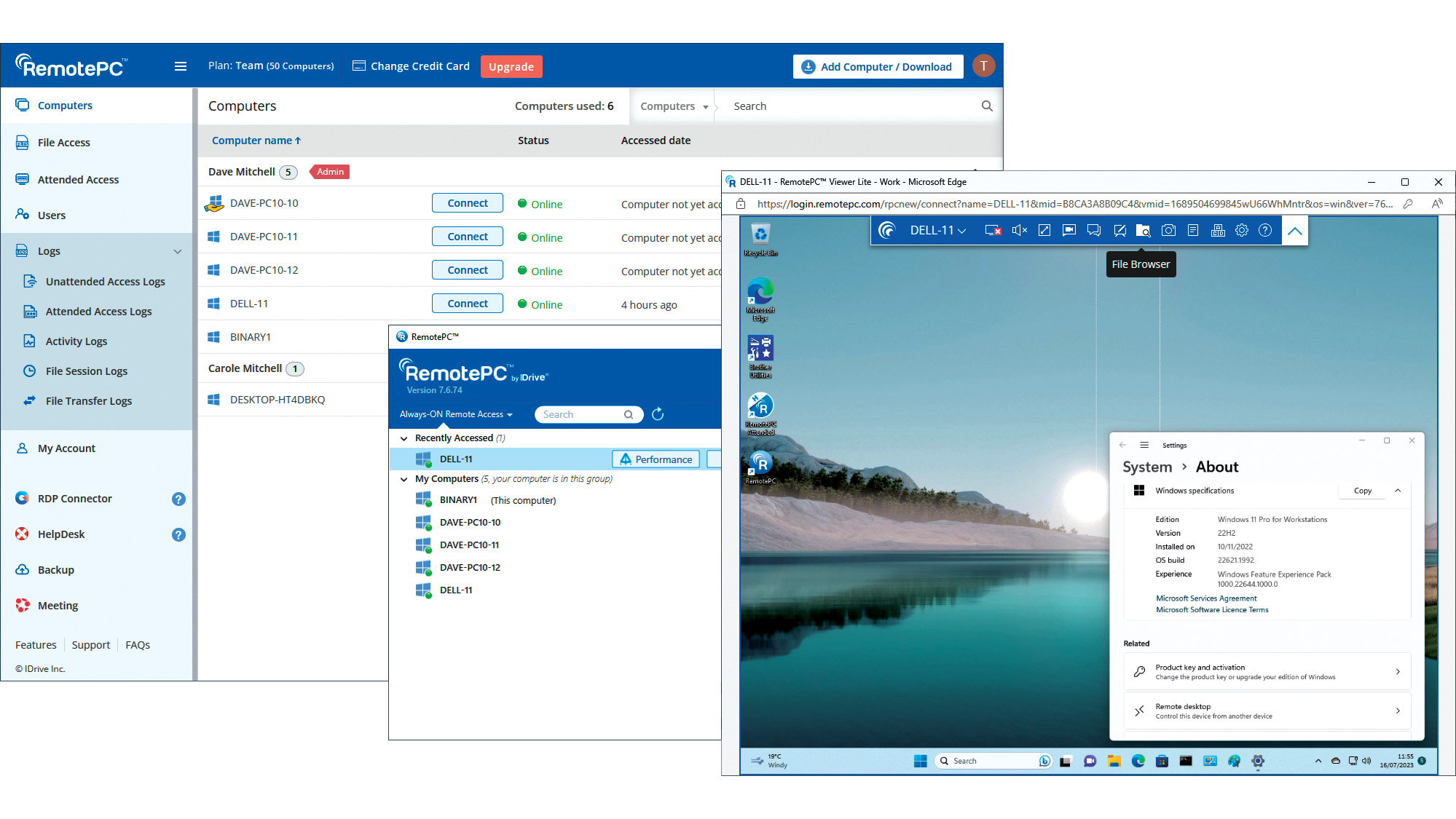 IDrive RemotePC Team (2023) review: Affordable cloud-hosted remote support
IDrive RemotePC Team (2023) review: Affordable cloud-hosted remote supportReviews Secure cloud-hosted remote support that's easy to use, rich in features and exceptional value for SMBs
-
 ZTNA vs on-premises VPN
ZTNA vs on-premises VPNWhitepaper How ZTNA wins the network security game
-
 Getting the best value from your remote support software
Getting the best value from your remote support softwareAdvertisement Feature Value is about much more than just the initial costs involved, so careful consideration must be given to any purchase
-
 Why you need a cloud solution for your remote support
Why you need a cloud solution for your remote supportAdvertisement Feature With distributed workforces and a broad user base, modern businesses are looking for modern software


