The human factor of endpoint security
Security systems are only effective if your workforce choose to use them.
In this video, the Head of HP's Security Lab Simon Shiu and HP Technical Sales Manager Neil Anderson explain how human beings are often the weakest link in system security, and what can be done to guard against this. Whilst some of this is about how systems are designed, education is also fundamentally important. This is where HP's video series The Wolf comes in. Starring Christian Slater, these videos dramatise how human beings and the way they use technology can be the conduit through which hackers gain access to a company's systems.
In particular, the way printers are used within a company can turn them into an endpoint through which hackers can gain access to further information. For example, a compromised multi-function printer can be used to capture data containing usernames and passwords, that in turn enables discovery of information regarding a stock listing. This then has financial implications for the fictional company in The Wolf video, but it's a threat that's all too real. This story provides very useful education about how company staff can avoid falling prey to phishing attacks that give hackers access to endpoints such as printers. But HP is also honing the user experience of its products to make all this more intuitive, so keeping things secure is even easier to achieve.
Find out how to make security easier for your workers.
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
ITPro is a global business technology website providing the latest news, analysis, and business insight for IT decision-makers. Whether it's cyber security, cloud computing, IT infrastructure, or business strategy, we aim to equip leaders with the data they need to make informed IT investments.
For regular updates delivered to your inbox and social feeds, be sure to sign up to our daily newsletter and follow on us LinkedIn and Twitter.
-
 Meta just revived plans to train AI models using European user data
Meta just revived plans to train AI models using European user dataNews Meta has confirmed plans to train AI models using European users’ public content and conversations with its Meta AI chatbot.
By Nicole Kobie
-
 AI is helping bad bots take over the internet
AI is helping bad bots take over the internetNews Automated bot traffic has surpassed human activity for the first time in a decade, according to Imperva
By Bobby Hellard
-
 Forget MFA fatigue, attackers are exploiting ‘click tolerance’ to trick users into infecting themselves with malware
Forget MFA fatigue, attackers are exploiting ‘click tolerance’ to trick users into infecting themselves with malwareNews Threat actors are exploiting users’ familiarity with verification tests to trick them into loading malware onto their systems, new research has warned.
By Solomon Klappholz
-
 Amazon confirms employee data compromised amid 2023 MOVEit breach claims – but the hacker behind the leak says a host of other big tech names are also implicated
Amazon confirms employee data compromised amid 2023 MOVEit breach claims – but the hacker behind the leak says a host of other big tech names are also implicatedNews Millions of records stolen during the 2023 MOVEit data breach have been leaked
By Solomon Klappholz
-
 Nearly 70 software vendors sign up to CISA’s cyber resilience program
Nearly 70 software vendors sign up to CISA’s cyber resilience programNews Major software manufacturers pledge to a voluntary framework aimed at boosting cyber resilience of customers across the US
By Solomon Klappholz
-
 Busting nine myths about file-based threats
Busting nine myths about file-based threatsWhitepaper Distinguish the difference between fact and fiction when it comes to preventing file-based threats
By ITPro
-
 The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standard
The Total Economic Impact™ of the Intel vPro® Platform as an endpoint standardWhitepaper Cost savings and business benefits enabled by the Intel vPro® Platform as an endpotnt standard
By ITPro
-
 The Total Economic Impact™ of IBM Security MaaS360 with Watson
The Total Economic Impact™ of IBM Security MaaS360 with WatsonWhitepaper Cost savings and business benefits enabled by MaaS360
By ITPro
-
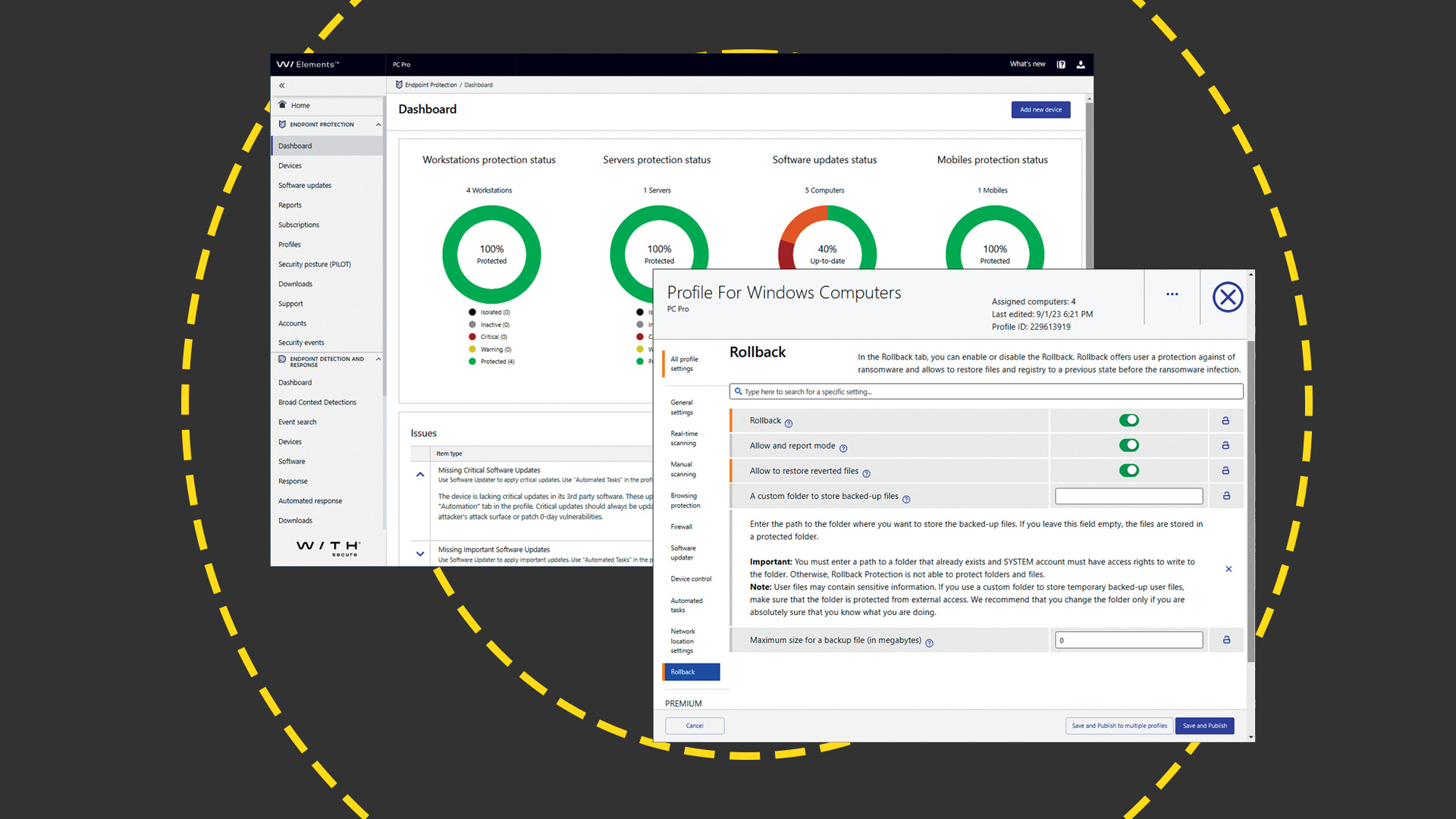 WithSecure Elements EPP and EDR review: Endpoint protection on a plate
WithSecure Elements EPP and EDR review: Endpoint protection on a plateReviews An affordable cloud-managed solution with smart automated remediation services
By Dave Mitchell
-
 KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023
KuppingerCole leadership compass report - Unified endpoint management (UEM) 2023Whitepaper Get an updated overview of vendors and their product offerings in the UEM market.
By ITPro
