Devastating hacking group expands focus to US power grid
The Xenotime hackers were previously responsible for the Triton malware that brought an oil and gas facility to its knees


Security researchers from Dragos have observed the hacking group Xenotime, known for highly effective malware attacks, has expanded its focus and is now probing the US power grid for possible entry points.
Xenotime is best known for its distribution of the 'Triton' malware back in 2017 which targeted industrial machinery and IoT devices, causing them to run unsafely, inflict physical damage to equipment and shut down production lines.
Dragos has been tracking Xenotime's activity for months and although the group has been known to target the oil and gas sector, the recent expansion into the electricity sector indicates a further investment of time and resources into breaking critical infrastructure.
The researchers said that the amount of resources required to carry out probes of this scale previously limited the number of threat actors which were capable of such attacks, but success breeds interest from other parties too.
"The high resource requirement previously limited such attacks to a few potential adversaries, but as more players see value and interest in targeting critical infrastructure - and those already invested see dividends from their behaviours - the threat landscape grows," said Dragos.
Since the group's shift into the electricity sector in February, it's believed the probes haven't been successful or caused any power outages, but Dragos stressed the importance of understanding the group's methodologies for all industrial control system (ICS) operators.
"A key element in defence against sophisticated, expanding threats is understanding threat behaviours and methodologies, beyond simply indicators of compromise," it said.
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Xenotime's scanning of the power grid shouldn't be considered a fully-fledged cyber attack just yet, by probing the network and looking for entry points, it could be seen as an attempt to 'test the waters' and see where weaknesses in the network lie before potentially launching a full-scale attack.
Although no malicious action has been taken yet, Xenotime's proven ability to launch devastating attacks should be cause for concern and also offers an insight into the future threat landscape as hackers move away from mere financial returns.
"Hackers work for many motives and goals. Those who are profit minded look for the most return for the least investment," said Sam Curry, chief security officer at Cybereason. "Those who aren't profit minded either want splash, and electrical power is showy, or they want options for the extension of politics by other means. However you slice it, the electrical grid is attractive to hackers."
Dragos said the activity observed thus far is in-line with the textbook plays attackers make before launching cyber attacks on ICS infrastructure. In addition to general network reconnaissance, Dragos observed incidents of credential stuffing to attempt authentication and using stolen usernames and passwords to force entry into user accounts.
"Ultimately, Xenotime's expansion to an additional ICS vertical is deeply concerning given this entity's willingness to undermine fundamental process safety in ICS environments placing lives and environments at great risk," said Dragos.
Xenotime's most notable attack was the distribution of a malware strain dubbed 'Triton' which forced a sophisticated oil and gas facility in the Middle East to shut down.
The malware caused industrial machinery to operate unsafely to the extent where it could have seriously injured human operators, so it was shut down and eventually, the entire facility halted operations.
The malware affected Safety Instrumented System (SIS) controllers, pieces of equipment designed to regulate safe machinery, and if faults are detected then the machine is safely taken offline by the SIS controller.
It was believed the malware was designed to reprogram the SIS controller and force it to allow machinery to continue running when unsafe, which could have caused the machine to break entirely or even cause actual harm to humans.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Why keeping track of AI assistants can be a tricky business
Why keeping track of AI assistants can be a tricky businessColumn Making the most of AI assistants means understanding what they can do – and what the workforce wants from them
By Stephen Pritchard
-
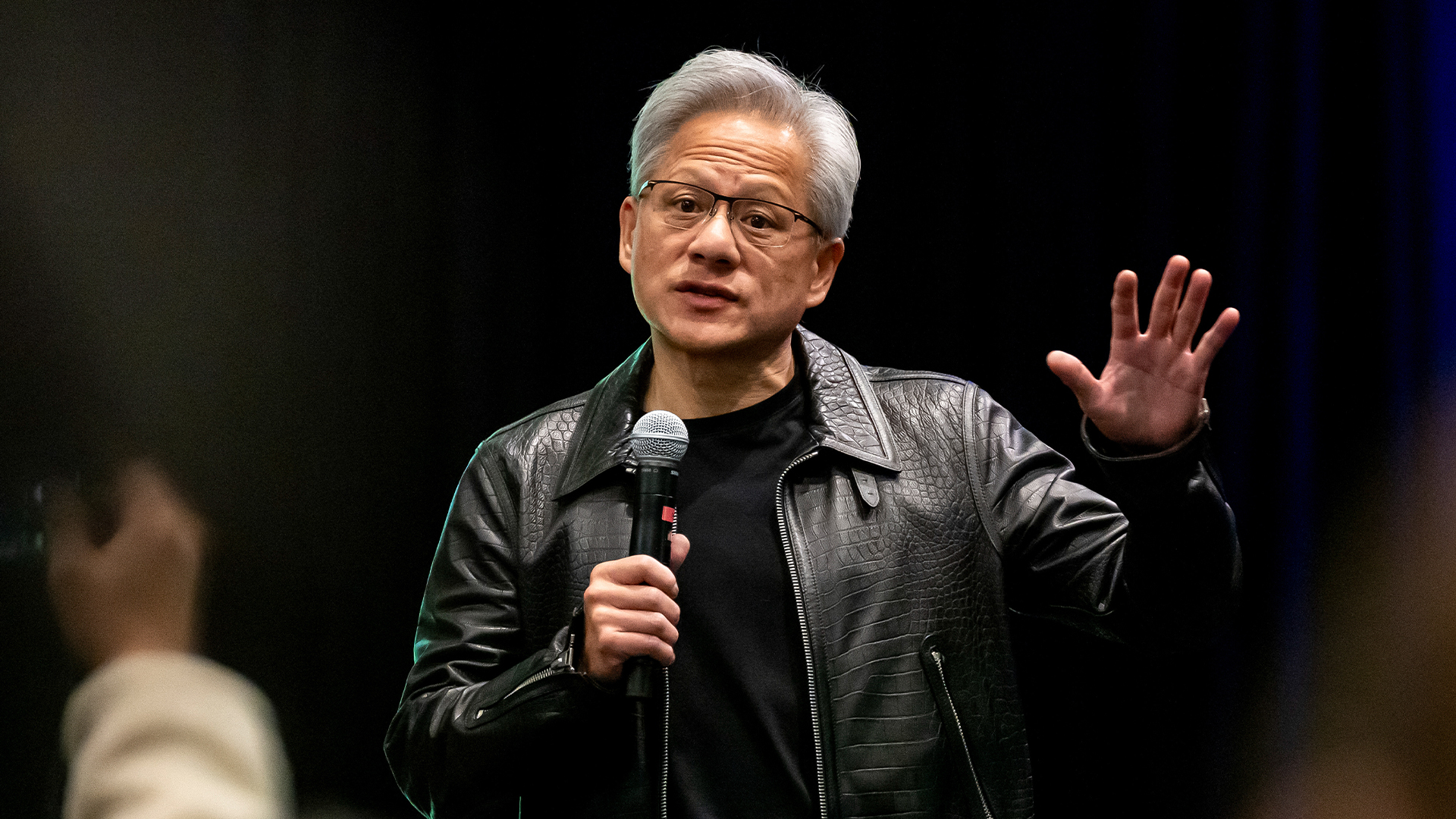 Nvidia braces for a $5.5 billion hit as tariffs reach the semiconductor industry
Nvidia braces for a $5.5 billion hit as tariffs reach the semiconductor industryNews The chipmaker says its H20 chips need a special license as its share price plummets
By Bobby Hellard