CISA issues fresh orders to polish security vulnerability detection in federal agencies
The move marks the latest step in the cyber security authority's ongoing ambition to minimise the government's exposure to attacks

The US Cybersecurity and Infrastructure Security Agency (CISA) has released a Binding Operational Directive (BOD) aimed at improving Federal Civilian Executive Branch (FCEB) agencies’ awareness of security vulnerabilities that may reside in their IT estates.
The BOD details its goals for building a sophisticated cyber defense in federal information systems. The guidelines further the US' sustained efforts in limiting federal agencies’ exposure to cyber attacks.
A catalog of Known Exploited Vulnerabilities (KEVs) that CISA began compiling back in November 2021 has been consistently updated and mandates FCEB agencies patch against a list of the most-exploited security vulnerabilities.
RELATED RESOURCE
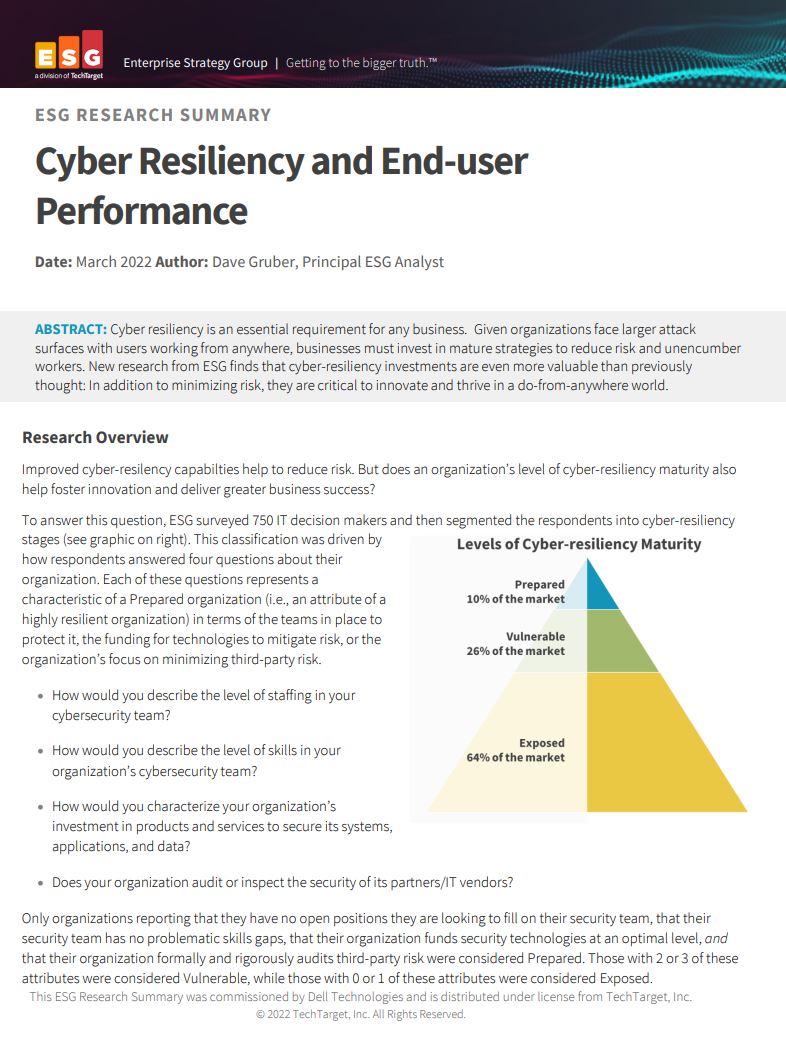
Cyber resiliency and end-user performance
Reduce risk and deliver greater business success with cyber-resilience capabilities
“Continuous and comprehensive asset visibility is a basic pre-condition for any organization to effectively manage cybersecurity risk,” the agency said in a public-facing notice.
“Accurate and up-to-date accounting of assets residing on federal networks is also critical for CISA to effectively manage cyber security for the FCEB enterprise.”
By April 3 2023, CISA will require all FCEB agencies to adhere to a number of mandatory cyber security practises such as initiating automated asset discovery every seven days, performing vulnerability enumeration across all discovered assets every 14 days, and uploading vulnerability enumeration results into the continuous diagnostics and mitigation (CDM) agency dashboard within 72 hours of discovery.
Agencies will also be required to initiate on-demand asset discovery and vulnerability enumeration within 72 hours of receiving a CISA request, providing available results within seven days.
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
The requirements do not apply to statutory national security systems, including certain systems operated by the Department of Defense or the intelligence community.
Per the White House cyber security executive order, federal agencies and CISA will deploy an updated CDM dashboard configuration that will enable analysts to access object-level vulnerability enumeration data by April 3 2023.
Underscoring CISA’s actions, the BOD stated that “within six months of issuance, the agency will publish data requirements for agencies to provide machine-level vulnerability enumeration performance data in a common data schema.”
FCEB agencies will be required to make a progress report at six, 12, and 18-month intervals detailing any dependencies that may prevent them from meeting the Directive's requirements.
-
 Bigger salaries, more burnout: Is the CISO role in crisis?
Bigger salaries, more burnout: Is the CISO role in crisis?In-depth CISOs are more stressed than ever before – but why is this and what can be done?
By Kate O'Flaherty Published
-
 Cheap cyber crime kits can be bought on the dark web for less than $25
Cheap cyber crime kits can be bought on the dark web for less than $25News Research from NordVPN shows phishing kits are now widely available on the dark web and via messaging apps like Telegram, and are often selling for less than $25.
By Emma Woollacott Published
-
 Hackers are targeting Ivanti VPN users again – here’s what you need to know
Hackers are targeting Ivanti VPN users again – here’s what you need to knowNews Ivanti has re-patched a security flaw in its Connect Secure VPN appliances that's been exploited by a China-linked espionage group since at least the middle of March.
By Emma Woollacott Published
-
 Broadcom issues urgent alert over three VMware zero-days
Broadcom issues urgent alert over three VMware zero-daysNews The firm says it has information to suggest all three are being exploited in the wild
By Solomon Klappholz Published
-
 Nakivo backup flaw still present on some systems months after firms’ ‘silent patch’, researchers claim
Nakivo backup flaw still present on some systems months after firms’ ‘silent patch’, researchers claimNews Over 200 vulnerable Nakivo backup instances have been identified months after the firm silently patched a security flaw.
By Solomon Klappholz Published
-
 Everything you need to know about the Microsoft Power Pages vulnerability
Everything you need to know about the Microsoft Power Pages vulnerabilityNews A severe Microsoft Power Pages vulnerability has been fixed after cyber criminals were found to have been exploiting unpatched systems in the wild.
By Solomon Klappholz Published
-
 Vulnerability management complexity is leaving enterprises at serious risk
Vulnerability management complexity is leaving enterprises at serious riskNews Fragmented data and siloed processes mean remediation is taking too long
By Emma Woollacott Published
-
 A critical Ivanti flaw is being exploited in the wild – here’s what you need to know
A critical Ivanti flaw is being exploited in the wild – here’s what you need to knowNews Cyber criminals are actively exploiting a critical RCE flaw affecting Ivanti Connect Secure appliances
By Solomon Klappholz Published
-
 Researchers claim an AMD security flaw could let hackers access encrypted data
Researchers claim an AMD security flaw could let hackers access encrypted dataNews Using only a $10 test rig, researchers were able to pull off the badRAM attack
By Solomon Klappholz Published
-
 A journey to cyber resilience
A journey to cyber resiliencewhitepaper DORA: Ushering in a new era of cyber security
By ITPro Published