5 Steps to Prioritize Based on Risk with Snyk


Risk-based prioritization allows organizations to gain insights into which vulnerabilities affect their most business-critical applications, allowing teams to prioritize fixing vulnerabilities that have the greatest impact.
This cheat sheet gives you five simple steps to protect your most important application assets and prioritize issues based on the actual risk to your organization. Learn more about how Snyk can help you focus on the security concerns that truly matter.
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
ITPro is a global business technology website providing the latest news, analysis, and business insight for IT decision-makers. Whether it's cyber security, cloud computing, IT infrastructure, or business strategy, we aim to equip leaders with the data they need to make informed IT investments.
For regular updates delivered to your inbox and social feeds, be sure to sign up to our daily newsletter and follow on us LinkedIn and Twitter.
-
 Beyond the Vulnerability Backlog: Building Risk-Based AppSec Programs
Beyond the Vulnerability Backlog: Building Risk-Based AppSec ProgramsBy ITPro
-
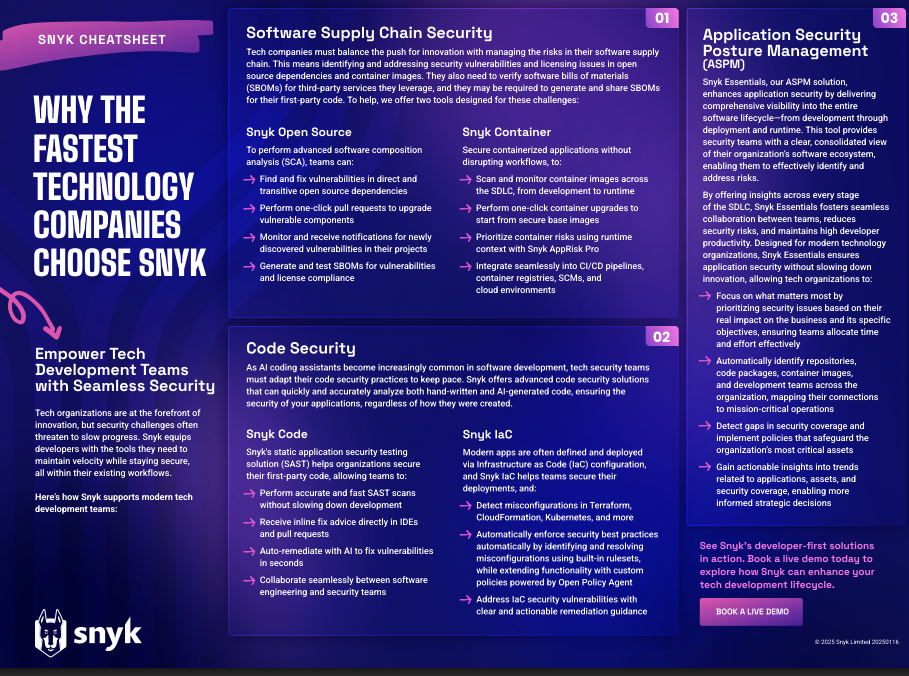 Why the Fastest Technology Companies choose Snyk Cheat Sheet
Why the Fastest Technology Companies choose Snyk Cheat SheetBy ITPro
-
 6 steps to a stronger security posture through automation
6 steps to a stronger security posture through automationBy ITPro
-
 IT & Security: The Critical Alliance Against Cyber Threats
IT & Security: The Critical Alliance Against Cyber ThreatsWhitepaper Actionable tips for creating a unified defense
By ITPro
-
 Device Management Is a Losing Battle
Device Management Is a Losing BattleWhitepaper Discover the winning strategy to regain control
By ITPro
-
 Stronger Together: Why IT-Security Collaboration Drives Greater Security and Efficiency
Stronger Together: Why IT-Security Collaboration Drives Greater Security and EfficiencyWhitepaper Discover why unification is the key to scalable, consistent security
By ITPro
-
 ‘Insiders don’t need to break in’: A developer crippled company networks with malicious code and a ‘kill switch’ after being sacked – and experts warn it shows the huge danger of insider threats
‘Insiders don’t need to break in’: A developer crippled company networks with malicious code and a ‘kill switch’ after being sacked – and experts warn it shows the huge danger of insider threatsNews Security experts have warned ITPro over the risks of insider threats from disgruntled workers after a software developer deployed a 'kill switch' to sabotage his former employer’s networks.
By Ross Kelly
-
 Developer security best practices in a fast growing tech company
Developer security best practices in a fast growing tech companyWhitepaper A buyer's guide for meeting the unprecedented speed and complexity of today's development practices
By ITPro
