Access brokers are making it easier for ransomware operators to attack businesses
A new business model has been uncovered that makes it much easier for attackers to gain access to business' networks


Cyber security researchers have uncovered a new underground business model dubbed 'access-as-a-service' in which access to an organisation's network is sold rather than an exploit or zero-day vulnerability.
So-called access brokers are selling direct access to a company's network in which they're already embedded via shared remote VPN connections. Attackers can pay different sums for varying levels of access.
The business model, discovered and detailed by Trend Micro, could lead to a new way for ransomware operators to launch attacks without having working exploit themselves.
Attackers are now able to buy their way into a network, paying only as much as they need for the right level of access to achieve their objective.
The business model relies on stolen credentials for access brokers to have a viable service and Trend Micro said businesses will have to place a greater emphasis on protecting credential theft to avoid future breaches.
"Access brokers in the criminal underground often advertise this service like it’s a cinema ticket: Somebody buys this ticket, and they get straight in," read the report. "In reality, however, things are a bit different.
RELATED RESOURCE

The best defence against ransomware
How ransomware is evolving and how to defend against it
"For example, what exactly do customers get in exchange for their money? Sometimes, it’s access to a web shell or a similar straightforward method of getting a command prompt into the compromised network. More often than not, however, it’s just a set of credentials and a VPN server to connect to."
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Remote Desktop Protocol (RDP) access and VPN-based access were the two most common products being advertised, primarily in the United States, Spain, Germany, France, and the UK.
After viewing more than a thousand adverts for services online, the most common targets Trend Micro observed were universities and schools (36%), 11% offered access to manufacturing firms and professional services, with other miscellaneous companies comprising the remainder.
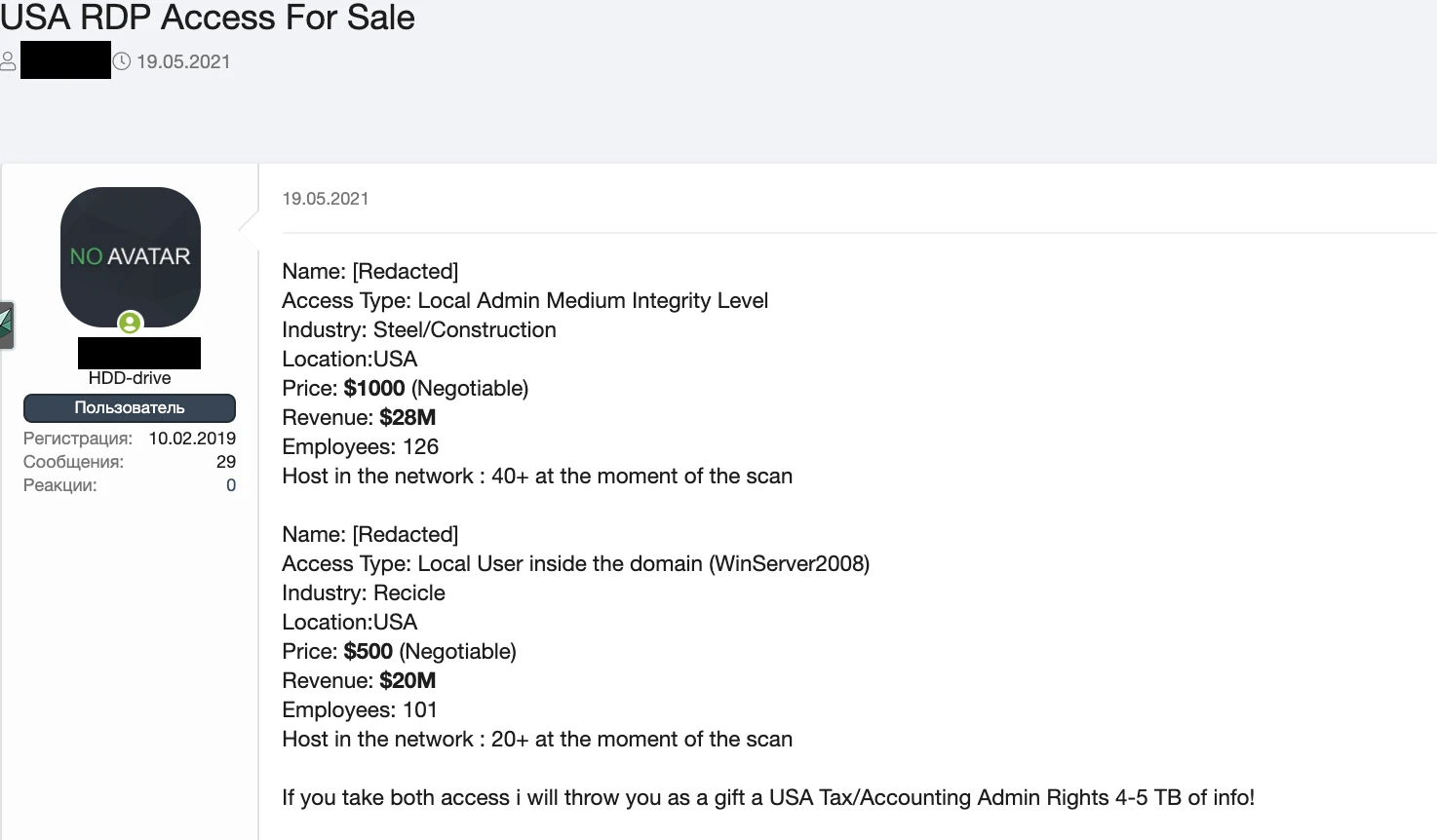
Online adverts typically offer access to a company with a broad description such as 'big German energy company', offer details of the level of access available, type of access on offer (RDP or VPN), cost of the service, and in some cases details of the company's turnover and employee numbers.

Prices for services can range between a few US dollars for access to a single machine and six-digit sums for admin credentials to an entire business, but most dedicated brokers don't advertise their prices openly, according to the researchers.
Access brokers are typically advertising their products either on deep web criminal marketplaces, through a network of connections throughout underground forums, and in less common cases dedicated online shops are used for smaller-scale, single-machine access.
Trend Micro made several suggestions for businesses wary of being exploited using this new business model. Monitoring public breaches can be useful in determining if credentials may have been stolen and triggering a password reset for all staff if one is detected.
Enabling two-factor authentication (2FA) for remote staff will also help prevent remote access from criminals, as will closely monitoring user behaviour on the network.
For the most cautious, operating on a zero-trust model and assuming all staff have lost their passwords to criminals before is recommended, applying the necessary security measures where appropriate.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Cleo attack victim list grows as Hertz confirms customer data stolen
Cleo attack victim list grows as Hertz confirms customer data stolenNews Hertz has confirmed it suffered a data breach as a result of the Cleo zero-day vulnerability in late 2024, with the car rental giant warning that customer data was stolen.
By Ross Kelly
-
 Lateral moves in tech: Why leaders should support employee mobility
Lateral moves in tech: Why leaders should support employee mobilityIn-depth Encouraging staff to switch roles can have long-term benefits for skills in the tech sector
By Keri Allan
-
 Cleo attack victim list grows as Hertz confirms customer data stolen – and security experts say it won't be the last
Cleo attack victim list grows as Hertz confirms customer data stolen – and security experts say it won't be the lastNews Hertz has confirmed it suffered a data breach as a result of the Cleo zero-day vulnerability in late 2024, with the car rental giant warning that customer data was stolen.
By Ross Kelly
-
 ‘Phishing kits are a force multiplier': Cheap cyber crime kits can be bought on the dark web for less than $25 – and experts warn it’s lowering the barrier of entry for amateur hackers
‘Phishing kits are a force multiplier': Cheap cyber crime kits can be bought on the dark web for less than $25 – and experts warn it’s lowering the barrier of entry for amateur hackersNews Research from NordVPN shows phishing kits are now widely available on the dark web and via messaging apps like Telegram, and are often selling for less than $25.
By Emma Woollacott
-
 Healthcare systems are rife with exploits — and ransomware gangs have noticed
Healthcare systems are rife with exploits — and ransomware gangs have noticedNews Nearly nine-in-ten healthcare organizations have medical devices that are vulnerable to exploits, and ransomware groups are taking notice.
By Nicole Kobie
-
 Alleged LockBit developer extradited to the US
Alleged LockBit developer extradited to the USNews A Russian-Israeli man has been extradited to the US amid accusations of being a key LockBit ransomware developer.
By Emma Woollacott
-
 February was the worst month on record for ransomware attacks – and one threat group had a field day
February was the worst month on record for ransomware attacks – and one threat group had a field dayNews February 2025 was the worst month on record for the number of ransomware attacks, according to new research from Bitdefender.
By Emma Woollacott
-
 CISA issues warning over Medusa ransomware after 300 victims from critical sectors impacted
CISA issues warning over Medusa ransomware after 300 victims from critical sectors impactedNews The Medusa ransomware as a Service operation compromised twice as many organizations at the start of 2025 compared to 2024
By Solomon Klappholz
-
 Warning issued over prolific 'Ghost' ransomware group
Warning issued over prolific 'Ghost' ransomware groupNews The Ghost ransomware group is known to act fast and exploit vulnerabilities in public-facing appliances
By Solomon Klappholz
-
 The Zservers takedown is another big win for law enforcement
The Zservers takedown is another big win for law enforcementNews LockBit has been dealt another blow by law enforcement after Dutch police took 127 of its servers offline
By Solomon Klappholz