How targeted simulations differ from penetration tests and vulnerability scanning
Stay one step ahead of cyber attackers


As cyberattacks become more sophisticated, they become harder to detect and mitigate. Current methods that organisations use to verify that their systems and data are protected are vulnerability scans and penetration tests, neither of which present the full picture of an organisation’s security posture.
The most effective way for an organisation to test its resilience against the growing wave of cybercrime is to opt for targeted attack simulations that use multi-vector simulated attacks. These kinds of simulations are known as Breach and Attack Simulations (BAS).
This whitepaper evaluates the effectiveness of a holistic BAS strategy compared to traditional methods of gaining insight into the security posture of an organisation.
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
ITPro is a global business technology website providing the latest news, analysis, and business insight for IT decision-makers. Whether it's cyber security, cloud computing, IT infrastructure, or business strategy, we aim to equip leaders with the data they need to make informed IT investments.
For regular updates delivered to your inbox and social feeds, be sure to sign up to our daily newsletter and follow on us LinkedIn and Twitter.
-
 Cleo attack victim list grows as Hertz confirms customer data stolen
Cleo attack victim list grows as Hertz confirms customer data stolenNews Hertz has confirmed it suffered a data breach as a result of the Cleo zero-day vulnerability in late 2024, with the car rental giant warning that customer data was stolen.
By Ross Kelly
-
 Lateral moves in tech: Why leaders should support employee mobility
Lateral moves in tech: Why leaders should support employee mobilityIn-depth Encouraging staff to switch roles can have long-term benefits for skills in the tech sector
By Keri Allan
-
 Bugcrowd’s new MSP program looks to transform pen testing for small businesses
Bugcrowd’s new MSP program looks to transform pen testing for small businessesNews Cybersecurity provider Bugcrowd has launched a new service aimed at helping MSP’s drive pen testing capabilities - with a particular focus on small businesses.
By Ross Kelly
-
 Building a new approach to security with the next generation of penetration testing
Building a new approach to security with the next generation of penetration testingSponsored Combining human-led testing with continuous automated scanning can elevate your security regime
By ITPro
-
 OpenAI to pay up to $20k in rewards through new bug bounty program
OpenAI to pay up to $20k in rewards through new bug bounty programNews The move follows a period of unrest over data security concerns
By Ross Kelly
-
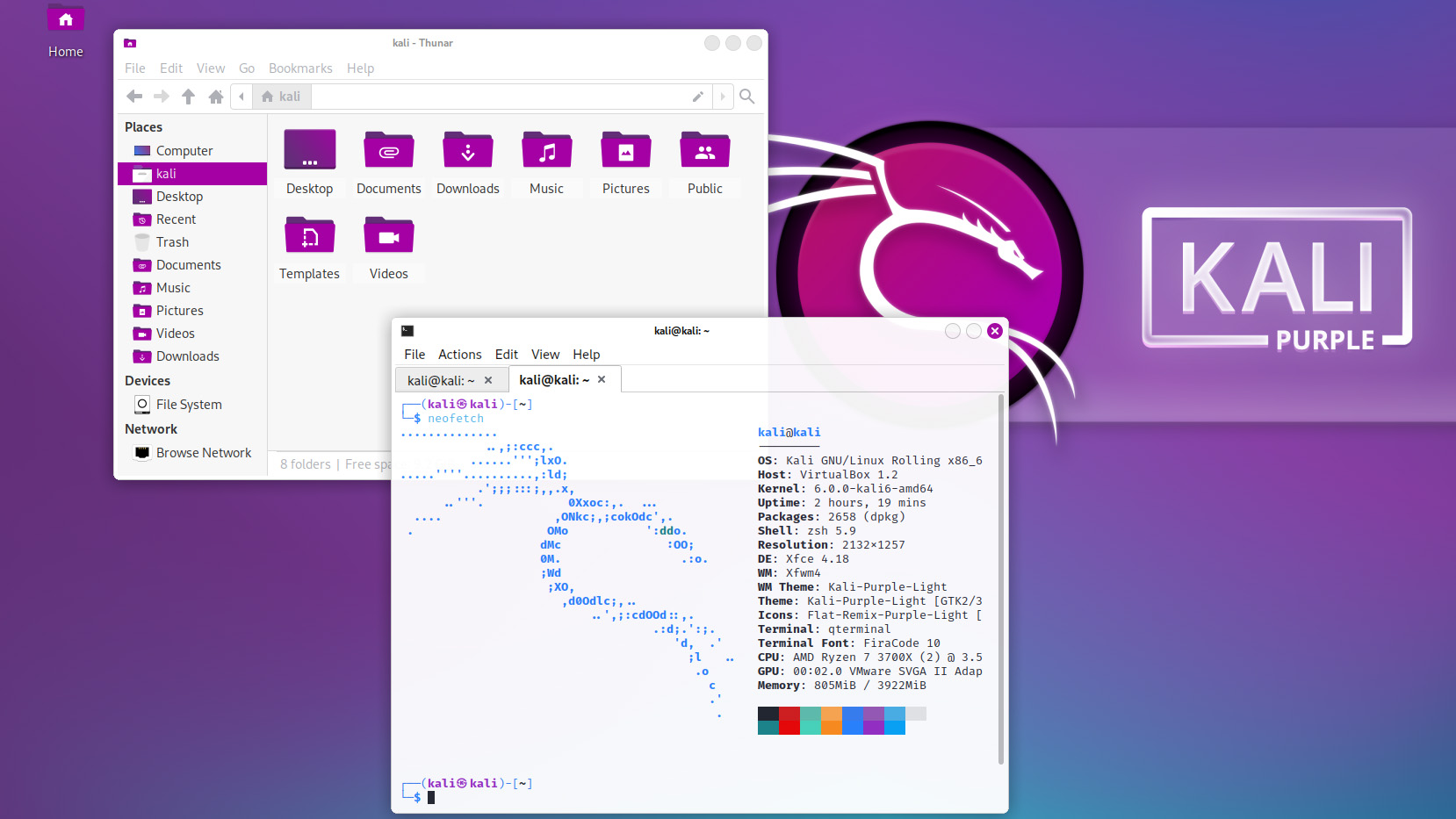 Kali Linux releases first-ever defensive distro with score of new tools
Kali Linux releases first-ever defensive distro with score of new toolsNews Kali Purple marks the next step for the red-teaming platform on the project's tenth anniversary
By Rory Bathgate
-
 Podcast transcript: Meet the cyborg hacker
Podcast transcript: Meet the cyborg hackerIT Pro Podcast Read the full transcript for this episode of the IT Pro Podcast
By IT Pro
-
 The IT Pro Podcast: Meet the cyborg hacker
The IT Pro Podcast: Meet the cyborg hackerIT Pro Podcast Resistance is futile - offensive biotech implants are already here
By IT Pro
-
 Russia-linked state-sponsored hackers launch fresh attacks by abusing latest red team tool
Russia-linked state-sponsored hackers launch fresh attacks by abusing latest red team toolNews Researchers said the new tool has evaded the detection of many leading security products and is quickly growing in popularity
By Connor Jones
-
 Train firm slammed over 'bonus' phishing test
Train firm slammed over 'bonus' phishing testNews Security experts suggest businesses use other 'lures' to avoid upsetting workers in the current climate
By Bobby Hellard