GitHub alerts users to active phishing campaign
The attack revolves around counterfeit CircleCI notifications urging users to accept updated terms of use and privacy policy

GitHub has notified its users of a phishing campaign active since 16 September.
The bait in the seemingly persuasive phishing campaign is an email that mimics notifications from continuous integration and delivery platform CircleCI.
RELATED RESOURCE
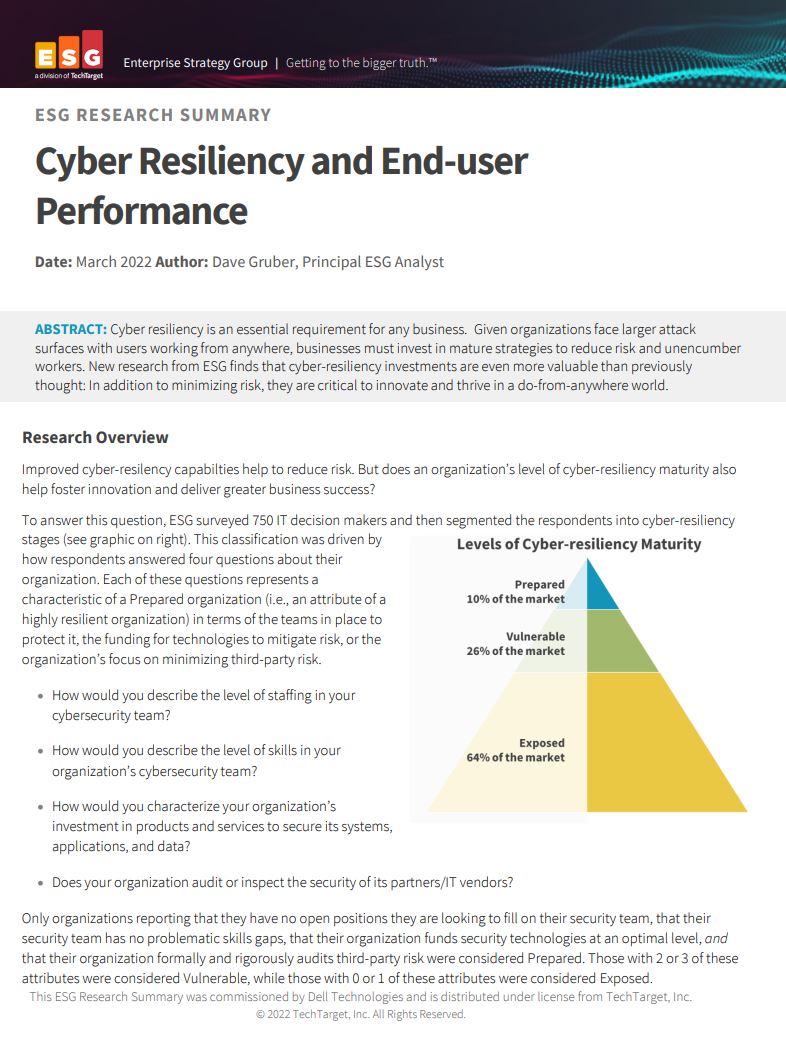
Cyber resiliency and end-user performance
Reduce risk and deliver greater business success with cyber-resilience capabilities
Specifically, the fake email coerces recipients to accept updated “user terms and privacy policy” by signing into their GitHub accounts again through CircleCI.
“As part of our integration with GitHub, we are updating our Terms of Use and Privacy Policy to provide greater transparency about how CircleCI uses your information, as well as how cookies are used to make our services more convenient and effective,” the email reads.
By relaying credentials through reverse proxies, the threat actors attempted to steal GitHub account credentials, including two-factor authentication (2FA) codes.
However, GitHub assured accounts protected with hardware security keys for multi-factor authentication (MFA) are not susceptible to the attack.
“While GitHub itself was not affected, the campaign has impacted many victim organizations,” GitHub informed in an advisory on Wednesday.
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Corroborating GitHub’s alert, CircleCI took to its forums to warn users that the platform would never ask users to enter credentials to view changes in its terms of service.
“Any emails from CircleCI should only include links to circleci.com or its sub-domains,” stated CircleCI in its notice.
“If you believe you or someone on your team may have accidentally clicked a link in this email, please immediately rotate your credentials for both GitHub and CircleCI, and audit your systems for any unauthorized activity,” added the company.
-
 Bigger salaries, more burnout: Is the CISO role in crisis?
Bigger salaries, more burnout: Is the CISO role in crisis?In-depth CISOs are more stressed than ever before – but why is this and what can be done?
By Kate O'Flaherty Published
-
 Cheap cyber crime kits can be bought on the dark web for less than $25
Cheap cyber crime kits can be bought on the dark web for less than $25News Research from NordVPN shows phishing kits are now widely available on the dark web and via messaging apps like Telegram, and are often selling for less than $25.
By Emma Woollacott Published
-
 Hackers are targeting Ivanti VPN users again – here’s what you need to know
Hackers are targeting Ivanti VPN users again – here’s what you need to knowNews Ivanti has re-patched a security flaw in its Connect Secure VPN appliances that's been exploited by a China-linked espionage group since at least the middle of March.
By Emma Woollacott Published
-
 Broadcom issues urgent alert over three VMware zero-days
Broadcom issues urgent alert over three VMware zero-daysNews The firm says it has information to suggest all three are being exploited in the wild
By Solomon Klappholz Published
-
 Nakivo backup flaw still present on some systems months after firms’ ‘silent patch’, researchers claim
Nakivo backup flaw still present on some systems months after firms’ ‘silent patch’, researchers claimNews Over 200 vulnerable Nakivo backup instances have been identified months after the firm silently patched a security flaw.
By Solomon Klappholz Published
-
 Everything you need to know about the Microsoft Power Pages vulnerability
Everything you need to know about the Microsoft Power Pages vulnerabilityNews A severe Microsoft Power Pages vulnerability has been fixed after cyber criminals were found to have been exploiting unpatched systems in the wild.
By Solomon Klappholz Published
-
 Vulnerability management complexity is leaving enterprises at serious risk
Vulnerability management complexity is leaving enterprises at serious riskNews Fragmented data and siloed processes mean remediation is taking too long
By Emma Woollacott Published
-
 A critical Ivanti flaw is being exploited in the wild – here’s what you need to know
A critical Ivanti flaw is being exploited in the wild – here’s what you need to knowNews Cyber criminals are actively exploiting a critical RCE flaw affecting Ivanti Connect Secure appliances
By Solomon Klappholz Published
-
 Researchers claim an AMD security flaw could let hackers access encrypted data
Researchers claim an AMD security flaw could let hackers access encrypted dataNews Using only a $10 test rig, researchers were able to pull off the badRAM attack
By Solomon Klappholz Published
-
 A journey to cyber resilience
A journey to cyber resiliencewhitepaper DORA: Ushering in a new era of cyber security
By ITPro Published