Australian government-owned energy company hit by ransomware attack
CS Energy confirmed hackers infiltrated its corporate network but says the incident has not impacted electricity generation


An energy company owned by the Queensland government has confirmed it was hit by a ransomware attack over the weekend.
CS Energy confirmed it has suffered a ransomware attack that took place on Saturday 27 November. The company said the incident occurred on its corporate network but has not impacted electricity generation at its Callide and Kogan Creek power stations, adding that it continues to generate and dispatch electricity.
CS Energy is focusing on restoring the security of its network and supporting employees, customers, and business partners with any questions they have. CEO Andrew Bills revealed that the company contained the ransomware attack by segregating the corporate network from other internal networks and enacting business continuity processes.
The energy company has also notified relevant state and federal agencies and is working closely with them as well as other cyber security experts. It has contacted its retail customers to reassure them there will be no impact on their electricity supply.
“Unfortunately, cyber events are a growing trend in Australia and overseas,” said Bills. “This incident may have affected our corporate network, but we are fortunate to have a resilient and highly skilled workforce who remain focused on ensuring CS Energy continues to deliver electricity to Queenslanders.”
IT Pro has contacted CS Energy to find out more information about the attack.
RELATED RESOURCE
How to reduce the risk of phishing and ransomware
Top security concerns and tips for mitigation
News of the attack comes after the Australian government published its Ransomware Action Plan in mid-October, which revealed it was looking to introduce legislative reforms to ensure cyber criminals are held to account for their actions. It would also apply harsher penalties to those who engage in ransomware or target the country’s critical infrastructure. The plan underlines the need to mandate ransomware incident reporting to the government and adds it does not condone ransom payments being made to hackers.
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
Cyber crime in Australia increased by nearly 13% in the past year as more Australians increased their dependence on the internet to work remotely, access services, and communicate, the Australia Cyber Security Centre said in a report from September. Around a quarter of cyber incidents reported were associated with the country’s critical infrastructure or essential services, and it recorded a 15% increase in ransomware reports.
Zach Marzouk is a former ITPro, CloudPro, and ChannelPro staff writer, covering topics like security, privacy, worker rights, and startups, primarily in the Asia Pacific and the US regions. Zach joined ITPro in 2017 where he was introduced to the world of B2B technology as a junior staff writer, before he returned to Argentina in 2018, working in communications and as a copywriter. In 2021, he made his way back to ITPro as a staff writer during the pandemic, before joining the world of freelance in 2022.
-
 Why keeping track of AI assistants can be a tricky business
Why keeping track of AI assistants can be a tricky businessColumn Making the most of AI assistants means understanding what they can do – and what the workforce wants from them
By Stephen Pritchard
-
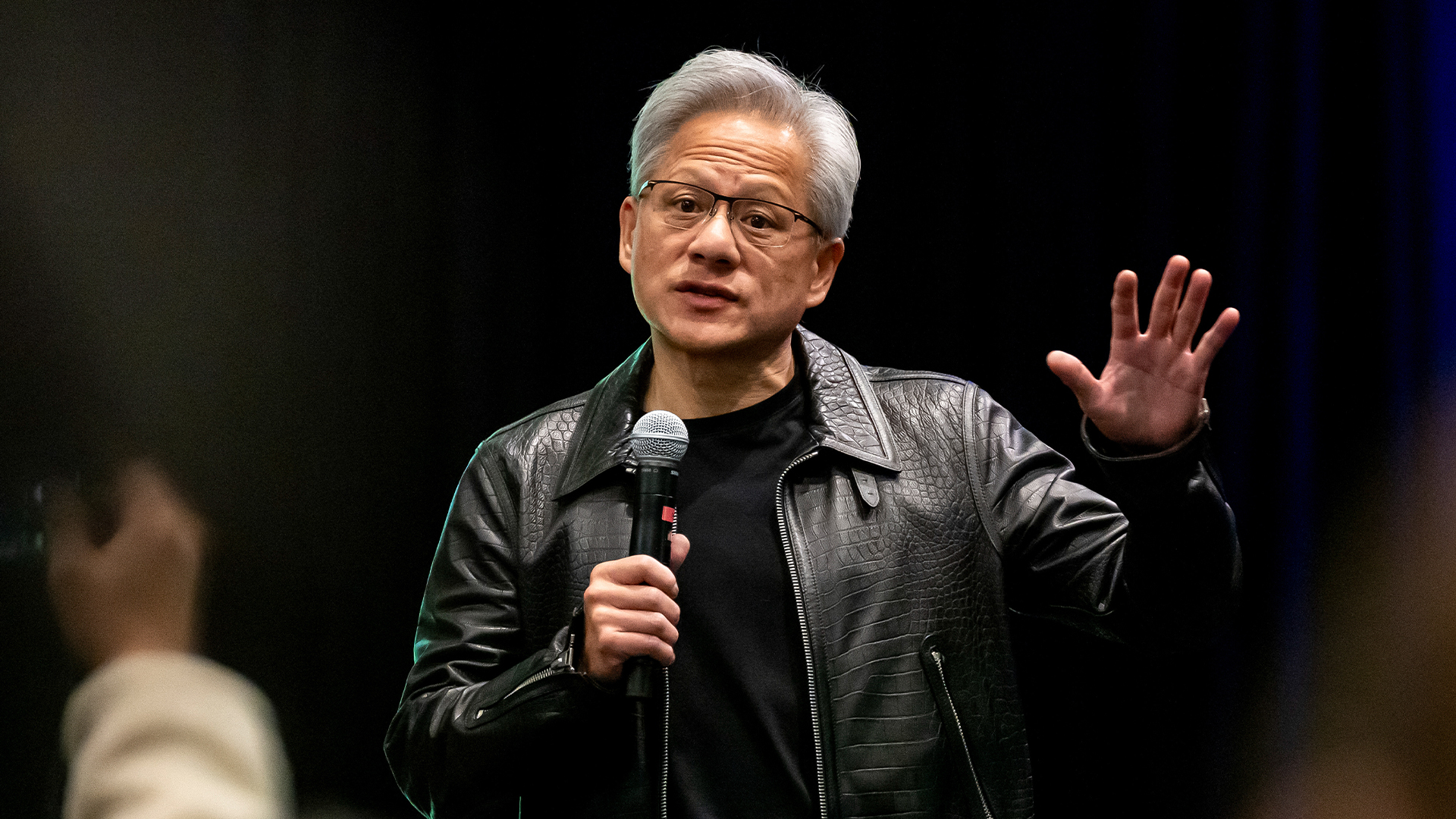 Nvidia braces for a $5.5 billion hit as tariffs reach the semiconductor industry
Nvidia braces for a $5.5 billion hit as tariffs reach the semiconductor industryNews The chipmaker says its H20 chips need a special license as its share price plummets
By Bobby Hellard
-
 Cleo attack victim list grows as Hertz confirms customer data stolen – and security experts say it won't be the last
Cleo attack victim list grows as Hertz confirms customer data stolen – and security experts say it won't be the lastNews Hertz has confirmed it suffered a data breach as a result of the Cleo zero-day vulnerability in late 2024, with the car rental giant warning that customer data was stolen.
By Ross Kelly
-
 ‘Phishing kits are a force multiplier': Cheap cyber crime kits can be bought on the dark web for less than $25 – and experts warn it’s lowering the barrier of entry for amateur hackers
‘Phishing kits are a force multiplier': Cheap cyber crime kits can be bought on the dark web for less than $25 – and experts warn it’s lowering the barrier of entry for amateur hackersNews Research from NordVPN shows phishing kits are now widely available on the dark web and via messaging apps like Telegram, and are often selling for less than $25.
By Emma Woollacott
-
 Healthcare systems are rife with exploits — and ransomware gangs have noticed
Healthcare systems are rife with exploits — and ransomware gangs have noticedNews Nearly nine-in-ten healthcare organizations have medical devices that are vulnerable to exploits, and ransomware groups are taking notice.
By Nicole Kobie
-
 Alleged LockBit developer extradited to the US
Alleged LockBit developer extradited to the USNews A Russian-Israeli man has been extradited to the US amid accusations of being a key LockBit ransomware developer.
By Emma Woollacott
-
 February was the worst month on record for ransomware attacks – and one threat group had a field day
February was the worst month on record for ransomware attacks – and one threat group had a field dayNews February 2025 was the worst month on record for the number of ransomware attacks, according to new research from Bitdefender.
By Emma Woollacott
-
 CISA issues warning over Medusa ransomware after 300 victims from critical sectors impacted
CISA issues warning over Medusa ransomware after 300 victims from critical sectors impactedNews The Medusa ransomware as a Service operation compromised twice as many organizations at the start of 2025 compared to 2024
By Solomon Klappholz
-
 Warning issued over prolific 'Ghost' ransomware group
Warning issued over prolific 'Ghost' ransomware groupNews The Ghost ransomware group is known to act fast and exploit vulnerabilities in public-facing appliances
By Solomon Klappholz
-
 The Zservers takedown is another big win for law enforcement
The Zservers takedown is another big win for law enforcementNews LockBit has been dealt another blow by law enforcement after Dutch police took 127 of its servers offline
By Solomon Klappholz