LockBit leaks 44GB of Royal Mail's data and sets fresh £33 million ransom
200 employees are believed to be affected with vaccine records, salary information, HR formal dismissal documents, and business contract documents all appearing to be included in the leak


The LockBit ransomware as a service group has published data allegedly belonging to Royal Mail International via its deep web blog, more than a month after the postal company confirmed the attack.
LockBit is also still demanding a ransom of £33 million - a sum considerably lower than the £65 million ransom originally demanded.
The leaked data was made available for download via a 44GB compressed 7-Zip file and a manifest of the file’s contents was also made available in a separate plaintext document.
An initial analysis of the documents appears to show a number of sensitive files relating to various corners of the business.
One employee’s HR records, including their first, second, and third disciplinary warning, and one detailing their ultimate dismissal, appeared to be included in the thousands of leaked files.
Other files alluded to salary and overtime payment information for various employees with their full names attached to the document. One file referred to ‘network layout’, and a number of files appeared to relate to contracts with various third parties.
A significant number of files came from one individual's OneDrive which appears to have been raided by the cyber criminals. It contained images, their own vaccine records, and other miscellaneous files.
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
IT Pro reached out to Royal Mail International to confirm the legitimacy of the documents included in the leak, but the company did not answer specific questions.
“Royal Mail is aware that an unauthorised third party has published some data allegedly obtained from our network,” it told IT Pro in a statement. “The cyber incident impacted a system concerned with shipping mail overseas.
“At this stage of the investigation, we believe that the vast majority of this data is made up of technical program files and administrative business data. All of the evidence suggests that this data contains no financial information or other sensitive customer information. We continue to work closely with law enforcement agencies.”
An examination of the file tree supplied by LockBit appears to confirm Royal Mail’s claims that most of the files are not sensitive in nature.
RELATED RESOURCE
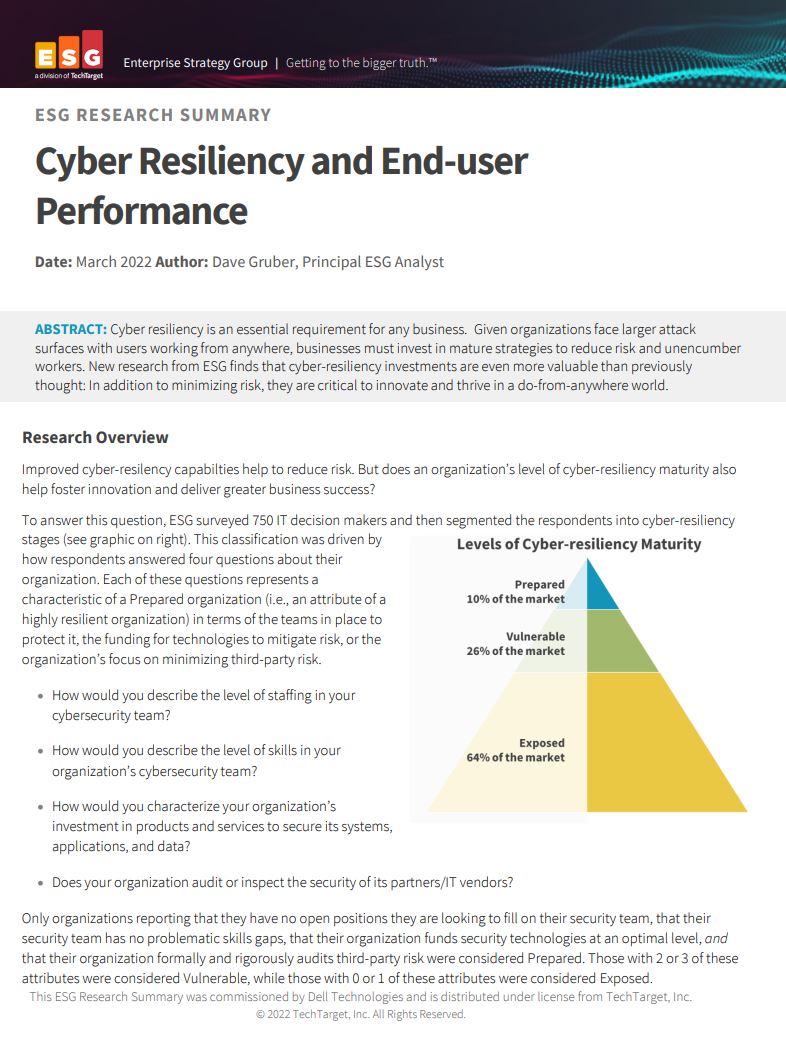
Cyber resiliency and end-user performance
Reduce risk and deliver greater business success with cyber-resilience capabilities
The company confirmed to the Telegraph that around 200 employees’ personal details were involved in the leak and that those affected have been informed.
It is unclear why LockBit still demands a ransom given it has now leaked the data on the company.
Royal Mail declined to answer when asked if LockBit had any additional data belonging to the company, or if it still required LockBit’s decryptor to fully restore its systems.
“International export services have been reinstated to all destinations for purchase through our shipping solutions and Post Office branches,” it told IT Pro. “We are now processing close to normal daily volumes of international export mail with some delays.”
LockBit has leaked the negotiation history with Royal Mail and thousands of files allegedly taken from its systems. Royal Mail also said it has recovered the point where it's operating close to normal daily volumes.
In usual cases this would be all the leverage a cyber criminal group would have over a victim, so why a ransom demand remains is unknown.
Unprecedented insight into ransomware negotiations
On 14 February, LockBit released the entire negotiation history between it and Royal Mail International, offering a rare insight into the negotiation tactics of the world’s leading ransomware operation.
It followed more than a month of negotiations which were most likely handled and strategised by the UK’s National Cyber Security Centre (NCSC) and National Crime Agency (NCA).
The transcript of the negotiations, which took place over instant text messages, showed the tactics deployed by UK authorities, such as trying to persuade LockBit to send files over to prove its decryptor worked.
LockBit caught on to the tactic which appeared to trick the cyber criminals into decrypting the files needed to make a full recovery without paying the ransom, which at the time was set at £65.7 million.
The ransom demands were later lowered to £57.4 million, but Royal Mail’s negotiator(s) said this was still far too great a sum to ever consider paying.
The NCSC’s longstanding advice is to never pay ransom demands and the negotiations never indicated that Royal Mail was ever willing to pay.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Bigger salaries, more burnout: Is the CISO role in crisis?
Bigger salaries, more burnout: Is the CISO role in crisis?In-depth CISOs are more stressed than ever before – but why is this and what can be done?
By Kate O'Flaherty Published
-
 Cheap cyber crime kits can be bought on the dark web for less than $25
Cheap cyber crime kits can be bought on the dark web for less than $25News Research from NordVPN shows phishing kits are now widely available on the dark web and via messaging apps like Telegram, and are often selling for less than $25.
By Emma Woollacott Published
-
 ‘Phishing kits are a force multiplier': Cheap cyber crime kits can be bought on the dark web for less than $25 – and experts warn it’s lowering the barrier of entry for amateur hackers
‘Phishing kits are a force multiplier': Cheap cyber crime kits can be bought on the dark web for less than $25 – and experts warn it’s lowering the barrier of entry for amateur hackersNews Research from NordVPN shows phishing kits are now widely available on the dark web and via messaging apps like Telegram, and are often selling for less than $25.
By Emma Woollacott Published
-
 Healthcare systems are rife with exploits — and ransomware gangs have noticed
Healthcare systems are rife with exploits — and ransomware gangs have noticedNews Nearly nine-in-ten healthcare organizations have medical devices that are vulnerable to exploits, and ransomware groups are taking notice.
By Nicole Kobie Published
-
 Alleged LockBit developer extradited to the US
Alleged LockBit developer extradited to the USNews A Russian-Israeli man has been extradited to the US amid accusations of being a key LockBit ransomware developer.
By Emma Woollacott Published
-
 February was the worst month on record for ransomware attacks – and one threat group had a field day
February was the worst month on record for ransomware attacks – and one threat group had a field dayNews February 2025 was the worst month on record for the number of ransomware attacks, according to new research from Bitdefender.
By Emma Woollacott Published
-
 CISA issues warning over Medusa ransomware after 300 victims from critical sectors impacted
CISA issues warning over Medusa ransomware after 300 victims from critical sectors impactedNews The Medusa ransomware as a Service operation compromised twice as many organizations at the start of 2025 compared to 2024
By Solomon Klappholz Published
-
 Warning issued over prolific 'Ghost' ransomware group
Warning issued over prolific 'Ghost' ransomware groupNews The Ghost ransomware group is known to act fast and exploit vulnerabilities in public-facing appliances
By Solomon Klappholz Published
-
 The Zservers takedown is another big win for law enforcement
The Zservers takedown is another big win for law enforcementNews LockBit has been dealt another blow by law enforcement after Dutch police took 127 of its servers offline
By Solomon Klappholz Published
-
 There’s a new ransomware player on the scene: the ‘BlackLock’ group has become one of the most prolific operators in the cyber crime industry – and researchers warn it’s only going to get worse for potential victims
There’s a new ransomware player on the scene: the ‘BlackLock’ group has become one of the most prolific operators in the cyber crime industry – and researchers warn it’s only going to get worse for potential victimsNews Security experts have warned the BlackLock group could become the most active ransomware operator in 2025
By Solomon Klappholz Published