Google’s Project Zero rolls out automatic 90-day disclosures
A raft of policy tweaks are aimed at instigating more thorough patch development and better patch adoption

Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
You are now subscribed
Your newsletter sign-up was successful
The Project Zero security team has expanded disclosure for all bugs to a full 90 days after first being flagged, even if the bug has been fixed early, as part of a number of changes to its policies and objectives.
Previously, its security researchers would disclose a bug that’s been flagged after 90 days have elapsed, or when the bug was fixed, at their discretion.
The Google-run team, however, is trialling 90-day disclosure by default, whether or not the bug has been fixed, unless a mutual agreement is reached between Project Zero and any vendor in concern.
Project Zero’s policy goals have also evolved beyond just ‘faster patch deployment’, to also encompass ‘thorough patch development’ and, among customers, ‘improved patch adoption’.
Extending the disclosure window to 90 days for bugs that have been fixed, meanwhile, will lead to incomplete fixes reported back, and compiled into the original bug report, as opposed to being filed under a new vulnerability. This was also previously done at the discretion of any particular researcher.
“We're constantly considering whether our policies are in the interest of user security, and we believe this change is a further step in the right direction,” said Project Zero manager Tim Willis. “We also think it's simple, consistent and fair.
“We want to make attacks using zero-day exploits more costly. We do this through the lens of offensive vulnerability research and evidence of how real attackers behave.
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
“This involves discovering and reporting a large number of security vulnerabilities, and through our experience with this work, we realised that faster patch development and patch deployment were very important and areas for industry improvement.”
The team has been at the heart of a string of significant bug disclosures of varying severity over the last few years, including, for example, the disclosure in 2018 of a significant Edge browser bug that Microsoft didn't fix within the 90-day window.
Project Zero’s core principles also came under review, with the team prioritising simplicity, consistency and fairness to different vendors, where some don’t get preferential treatment over others.
Its two new core objectives, thorough patch deployment and improved adoption, meanwhile are being added in conjunction to the full extension of the 90-day window as there were concerns that some companies fixed bugs by simply “papering over the cracks”.
By extending the disclosure window to a full 90 days for all bugs, including fixed bugs, Project Zero is hoping that the aim of ‘faster patch deployment’ will no longer lead to compromise on quality if there’s no need to rush getting fixes out.
As a result of extending disclosure to 90 days, researchers are hoping to see more iterative and through patching practices from vendors, and also improve patch adoption since Project Zero is incentivising vendors to offer updates to a large population within 90 days.

Keumars Afifi-Sabet is a writer and editor that specialises in public sector, cyber security, and cloud computing. He first joined ITPro as a staff writer in April 2018 and eventually became its Features Editor. Although a regular contributor to other tech sites in the past, these days you will find Keumars on LiveScience, where he runs its Technology section.
-
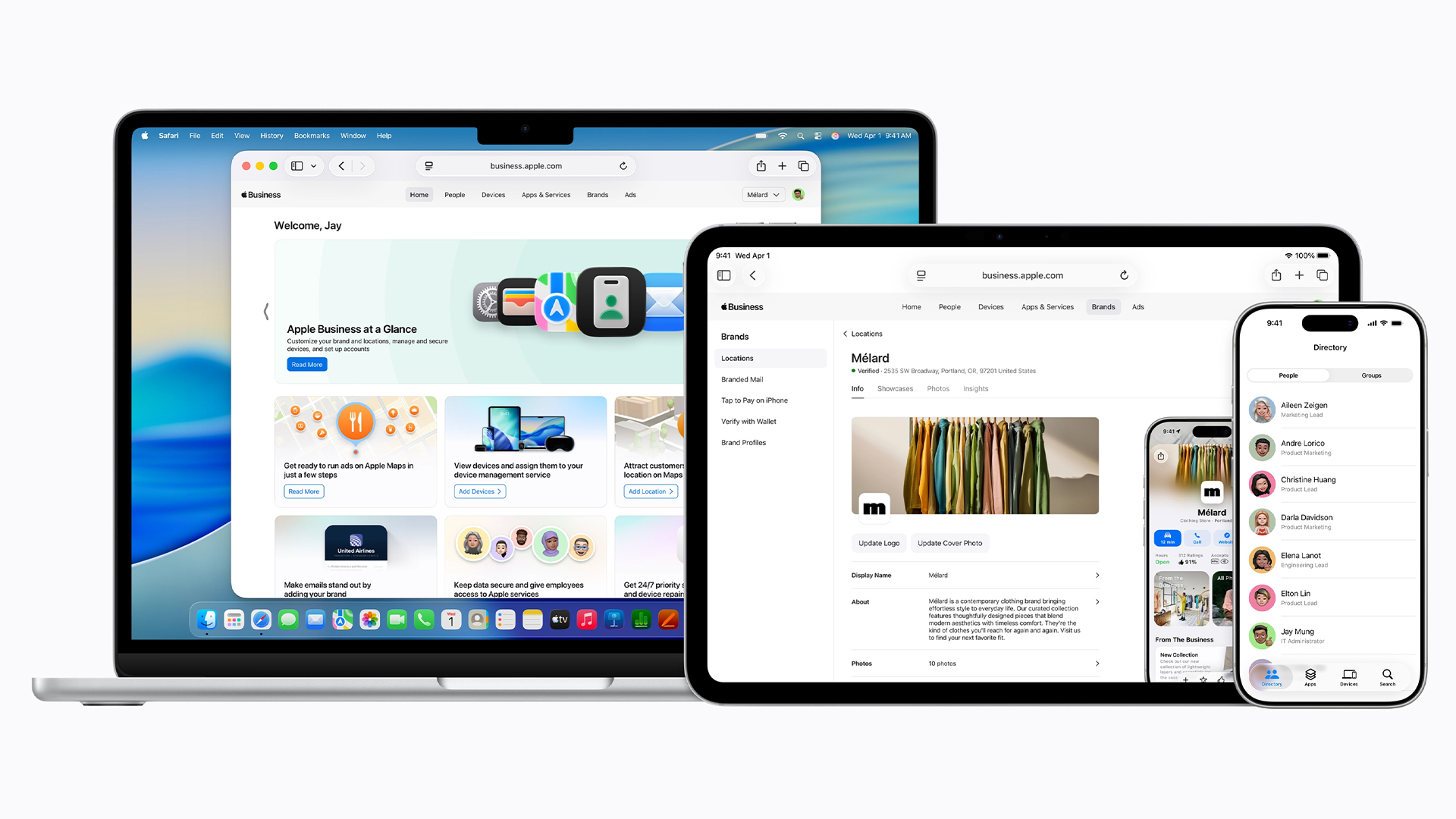 Everything you need to know about Apple Business
Everything you need to know about Apple BusinessNews The new platform will replace the previous business suites Apple offered, with more focus on helping businesses grow through Apple Maps
-
 UK firms regret software spending as tool sprawl causes IT headaches
UK firms regret software spending as tool sprawl causes IT headachesNews Spur-of-the-moment software purchases are creating fragmented tech stacks, and it’s harming productivity
-
 Ubuntu vulnerability exposes enterprises to root escalation, complete system compromise
Ubuntu vulnerability exposes enterprises to root escalation, complete system compromiseNews The high-severity Ubuntu vulnerability allows an unprivileged local attacker to escalate privileges through the interaction of two standard system components
-
 Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerability
Security agencies issue warning over critical Cisco Catalyst SD-WAN vulnerabilityNews Threat actors have been exploiting the vulnerability to achieve root access since 2023
-
 Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourself
Millions of developers could be impacted by flaws in Visual Studio Code extensions – here's what you need to know and how to protect yourselfNews The VS Code vulnerabilities highlight broader IDE security risks, said OX Security
-
 CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaught
CVEs are set to top 50,000 this year, marking a record high – here’s how CISOs and security teams can prepare for a looming onslaughtNews While the CVE figures might be daunting, they won't all be relevant to your organization
-
 Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to know
Microsoft patches six zero-days targeting Windows, Word, and more – here’s what you need to knowNews Patch Tuesday update targets large number of vulnerabilities already being used by attackers
-
 Experts welcome EU-led alternative to MITRE's vulnerability tracking scheme
Experts welcome EU-led alternative to MITRE's vulnerability tracking schemeNews The EU-led framework will reduce reliance on US-based MITRE vulnerability reporting database
-
 Veeam patches Backup & Replication vulnerabilities, urges users to update
Veeam patches Backup & Replication vulnerabilities, urges users to updateNews The vulnerabilities affect Veeam Backup & Replication 13.0.1.180 and all earlier version 13 builds – but not previous versions.
-
 Two Fortinet vulnerabilities are being exploited in the wild – patch now
Two Fortinet vulnerabilities are being exploited in the wild – patch nowNews Arctic Wolf and Rapid7 said security teams should act immediately to mitigate the Fortinet vulnerabilities