Apple patches 'superpower' zero-days affecting iPhones, iPads, and Macs
The RCE and kernel-level bugs may have been actively exploited and could give high-level privileges to attackers


Apple has fixed two zero-day vulnerabilities affecting iOS, iPadOS, and macOS Monterrey that may have been actively exploited.
The first exploit is a remote code execution (RCE) flaw affecting Apple’s proprietary browser engine WebKit, tracked as CVE-20220-32893.
An attacker could maliciously alter a web page and if visited by a WebKit-powered browser, then unauthorised code could run on unpatched devices.
WebKit is Apple’s browser engine and is naturally used to power the native Safari browser on currently supported iPhones and iPads. It’s also the engine that Apple compels app developers to use when building for its mobile devices.
This means even Google Chrome has to forfeit its Blink and V8 engines on iOS and iPadOS, and other browsers also have to use WebKit to pass Apple’s App Store checks.
Other apps that may not be browsers primarily, but have browsing features within them, also use WebKit to display web content which means the vulnerability may have a wide-reaching attack surface.
Devices affected by CVE-20220-32893 include iPhone 6s and later, iPad Pro (all models), iPad Air 2 and later, iPad 5th generation and later, iPad mini 4 and later, iPod touch (7th generation), and macOS Monterrey.
Get the ITPro daily newsletter
Sign up today and you will receive a free copy of our Future Focus 2025 report - the leading guidance on AI, cybersecurity and other IT challenges as per 700+ senior executives
This vulnerability is the third critical WebKit bug Apple has been made to fix this year after the first two patches were released within weeks of each other at the start of the year.
The second zero-day exploit patched by Apple on Wednesday is a kernel-level code execution bug that can be abused once an attacker gains an initial foothold on an affected device.
Tracked as CVE-2022-32894, one way an attacker could achieve that initial foothold is by exploiting the aforementioned WebKit flaw, according to researchers at Sophos.
This means an attacker “could jump from controlling just a single app on your device to taking over the operating system kernel itself, thus acquiring the sort of ‘administrative superpowers’ normally reserved for Apple itself,” said Paul Ducklin, principal research scientist at Sophos.
Such privileges could afford an attacker the ability to carry out activities such as spying on apps, accessing nearly all data on the device, retrieving locations, using cameras, taking screenshots, activating the microphone, and more, he said.
Like the WebKit flaw, the code required to exploit this vulnerability would have to be embedded within a maliciously crafted web page and executed after the WebKit vulnerability had already been exploited.
RELATED RESOURCE
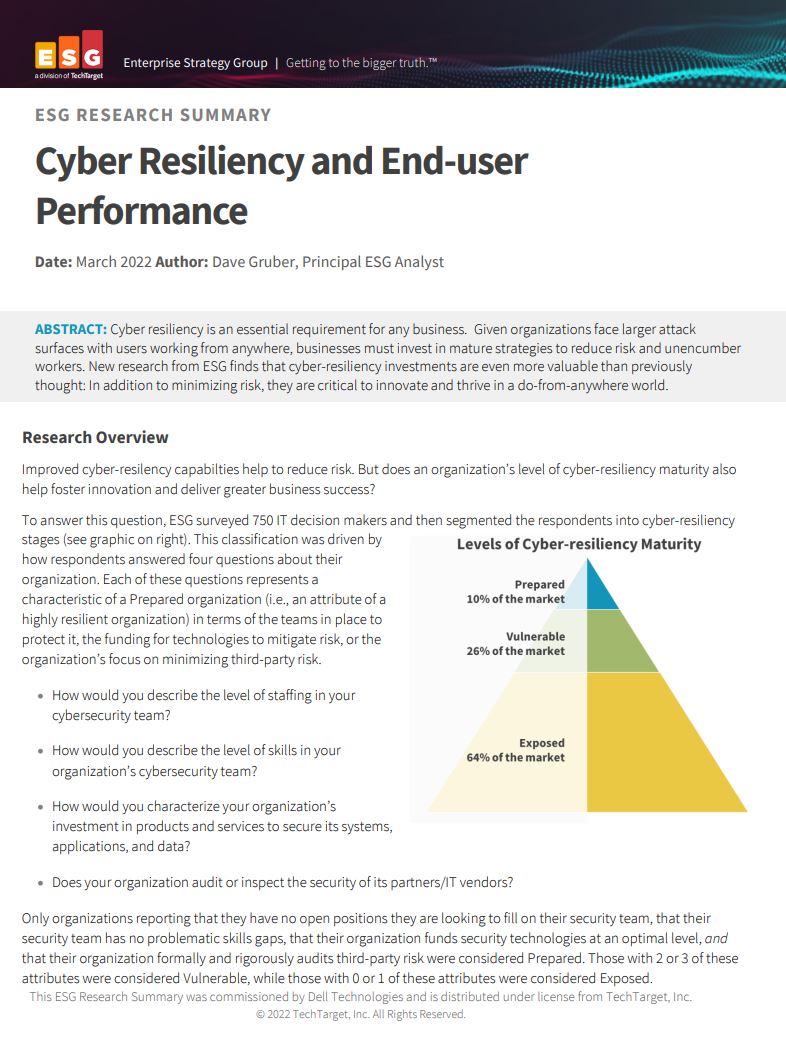
Cyber resiliency and end-user performance
Reduce risk and deliver greater business success with cyber-resilience capabilities
This zero-day also affects all the aforementioned iPhone and iPad devices, in addition to Macs running macOS Monterrey.
Both issues were caused by an out-of-bounds write issue and were addressed by improving the bounds checking of the vulnerable components.
The two vulnerabilities patched by Apple on Wednesday represent the sixth and seventh zero-day exploits that Apple has been forced to fix this year.
The company also patched a swathe of zero-day vulnerabilities in 2021 including the ForcedEntry exploit used by the notorious Pegasus spyware developed by NSO Group.

Connor Jones has been at the forefront of global cyber security news coverage for the past few years, breaking developments on major stories such as LockBit’s ransomware attack on Royal Mail International, and many others. He has also made sporadic appearances on the ITPro Podcast discussing topics from home desk setups all the way to hacking systems using prosthetic limbs. He has a master’s degree in Magazine Journalism from the University of Sheffield, and has previously written for the likes of Red Bull Esports and UNILAD tech during his career that started in 2015.
-
 Bigger salaries, more burnout: Is the CISO role in crisis?
Bigger salaries, more burnout: Is the CISO role in crisis?In-depth CISOs are more stressed than ever before – but why is this and what can be done?
By Kate O'Flaherty Published
-
 Cheap cyber crime kits can be bought on the dark web for less than $25
Cheap cyber crime kits can be bought on the dark web for less than $25News Research from NordVPN shows phishing kits are now widely available on the dark web and via messaging apps like Telegram, and are often selling for less than $25.
By Emma Woollacott Published
-
 Hackers are targeting Ivanti VPN users again – here’s what you need to know
Hackers are targeting Ivanti VPN users again – here’s what you need to knowNews Ivanti has re-patched a security flaw in its Connect Secure VPN appliances that's been exploited by a China-linked espionage group since at least the middle of March.
By Emma Woollacott Published
-
 Broadcom issues urgent alert over three VMware zero-days
Broadcom issues urgent alert over three VMware zero-daysNews The firm says it has information to suggest all three are being exploited in the wild
By Solomon Klappholz Published
-
 Nakivo backup flaw still present on some systems months after firms’ ‘silent patch’, researchers claim
Nakivo backup flaw still present on some systems months after firms’ ‘silent patch’, researchers claimNews Over 200 vulnerable Nakivo backup instances have been identified months after the firm silently patched a security flaw.
By Solomon Klappholz Published
-
 Everything you need to know about the Microsoft Power Pages vulnerability
Everything you need to know about the Microsoft Power Pages vulnerabilityNews A severe Microsoft Power Pages vulnerability has been fixed after cyber criminals were found to have been exploiting unpatched systems in the wild.
By Solomon Klappholz Published
-
 Vulnerability management complexity is leaving enterprises at serious risk
Vulnerability management complexity is leaving enterprises at serious riskNews Fragmented data and siloed processes mean remediation is taking too long
By Emma Woollacott Published
-
 A critical Ivanti flaw is being exploited in the wild – here’s what you need to know
A critical Ivanti flaw is being exploited in the wild – here’s what you need to knowNews Cyber criminals are actively exploiting a critical RCE flaw affecting Ivanti Connect Secure appliances
By Solomon Klappholz Published
-
 Researchers claim an AMD security flaw could let hackers access encrypted data
Researchers claim an AMD security flaw could let hackers access encrypted dataNews Using only a $10 test rig, researchers were able to pull off the badRAM attack
By Solomon Klappholz Published
-
 The threat prevention buyer's guide
The threat prevention buyer's guideWhitepaper Find the best advanced and file-based threat protection solution for you
By ITPro Published